The SCF CAP is an organization-level conformity assessment designed to utilize tailored cybersecurity and privacy controls that specifically address the applicable statutory, regulatory, and contractual obligations an Organization Seeking Assessment (OSA) is required to comply with. By using the metaframework nature of the SCF, an OSA is able to perform conformity assessments that span multiple cybersecurity and privacy-specific laws, regulations, and frameworks.
The SCF CAP exists to leverage SCF content to provide a company-level certification through a conformity assessment process. Earning a SCF Certified™ conformity designation is meant to signify a real accomplishment, not a “participation ribbon” that has little practical value for the OSA’s stakeholders to understand its overall security posture.
The SCF Council established the SCF CAP as a structure to conduct security, compliance, and resilience-related Third-Party Assessment, Attestation, and Certification (3PAAC) Services. While the SCF CAP shares similarities with single-focused certifications (e.g., ISO 27001, CMMC, FedRAMP), it is unique in its metaframework approach to covering multiple laws, regulations, and frameworks simultaneously.
The SCF CAP is designed to produce a deliverable Report on Conformity (ROC) with a designation that summarizes the organization’s overall security, compliance, and resilience program. It leverages concepts established in the Cybersecurity & Data Protection Assessment Standards (CDPAS).
The SCF CAP utilizes an examine, interview, and test assessment methodology to demonstrate conformity with multiple requirements simultaneously. This approach allows the SCF CAP to scale. For example, it can demonstrate conformity with NIST CSF, HIPAA, and EU GDPR as part of one engagement rather than three separate assessments.
The SCF CAP allows an organization to specify the applicable statutory, regulatory, and contractual obligations to establish a Minimum Security Requirements (MSR) control set. It leverages leading industry assessment practices to avoid reinventing assessment methodologies.
Download the SCF CAP BoK (PDF) for the complete assessment methodology, accreditation requirements, 3PAAC standards, and program structure.
The SCF CAP is designed for cybersecurity and privacy practitioners, by cybersecurity and data privacy practitioners. This concept is based on the need within the industry for a tailored conformity assessment solution capable of addressing several key considerations.
View compliance as a natural by-product of secure practices, not a standalone objective. The SCF CAP assesses real security posture across security, compliance, and resilience.
Scale to address multifaceted operational requirements across laws, regulations, and frameworks simultaneously. One assessment satisfies NIST CSF, HIPAA, GDPR, and more.
Acknowledge the stated risk tolerance of the OSA. The assessment adapts to the organization’s context using NIST-defined risk appetite, tolerance, and threshold distinctions.
Minimize the risk of “gaming” the certification process. The examine, interview, and test methodology ensures substantive evidence review with material control identification.
Supports Manual Point in Time (MPIT), Augmented Point in Time (APIT), and Augmented Evidence with Human Review (AEHR) assessment methods to reduce costs.
Based on NIST SP 2000-01 (ABC’s of Conformity Assessment), ISO/IEC 17000, ISO/IEC 17065, and CDPAS standards rather than reinventing assessment approaches.
The SCF CAP produces a Report on Conformity (ROC) that assigns one of four conformity designations based on assessment findings. Each control is designated as satisfactory, deficient, compensating, or not applicable.
The SCF CAP defines three levels of assessment rigor that determine the depth and scope of evidence evaluation:
Baseline assessment depth for organizations with lower risk profiles or initial certifications.
Deeper evidence review for organizations with moderate risk profiles or regulatory requirements demanding increased scrutiny.
Maximum assessment depth for high-risk profiles, critical infrastructure, or stringent regulatory obligations.
The SCF CAP supports three assessment methods that range from traditional manual assessments to technology-augmented continuous assessments:
Traditional methodology where evidence is manually reviewed at a specific point in time by the assessment team.
Automation augments the traditional methodology, using AI/autonomous technologies to compare desired state vs. current state via machine-readable configurations.
Ongoing, continuous control assessment where automation continuously evaluates controls with recurring human reviews to validate findings.
Cybersecurity Materiality & Material Controls
The SCF CAP incorporates cybersecurity materiality into the assessment process. Material controls are fundamental controls whose absence or failure exposes an organization to material impact. They cannot have compensating controls. The SCF designates material controls, material risks, material threats, and material incidents.
The SCF certification process consists of two primary phases that take the OSA from self-assessment through third-party validated certification.
The OSA conducts an internal self-assessment to evaluate control implementation against applicable SCF controls. This establishes the assessment boundary, defines the Statement of Applicability (SoA), identifies the MSR control set, and produces a first-party declaration of conformity status. The 1PD phase prepares the OSA by identifying gaps and establishing evidence before engaging a 3PAO.
A qualified 3PAO conducts the formal assessment using examine, interview, and test methodology. The 3PAO produces a Report on Conformity (ROC) consisting of a Technical Assessment Report (TAR) and Executive Assessment Report (EAR). Upon successful completion, the OSA receives the SCF Certified™ designation validated by The Cyber AB.
SCF Certified™ Options
Certifications are available in two forms: (1) LRF-Specific SCF Certification, certifying conformity against a specific authority (e.g., SCF Certified for NIST CSF 2.0); and (2) Tailored SCF Certification, certifying conformity against a custom MSR control set based on the OSA's specific obligations.
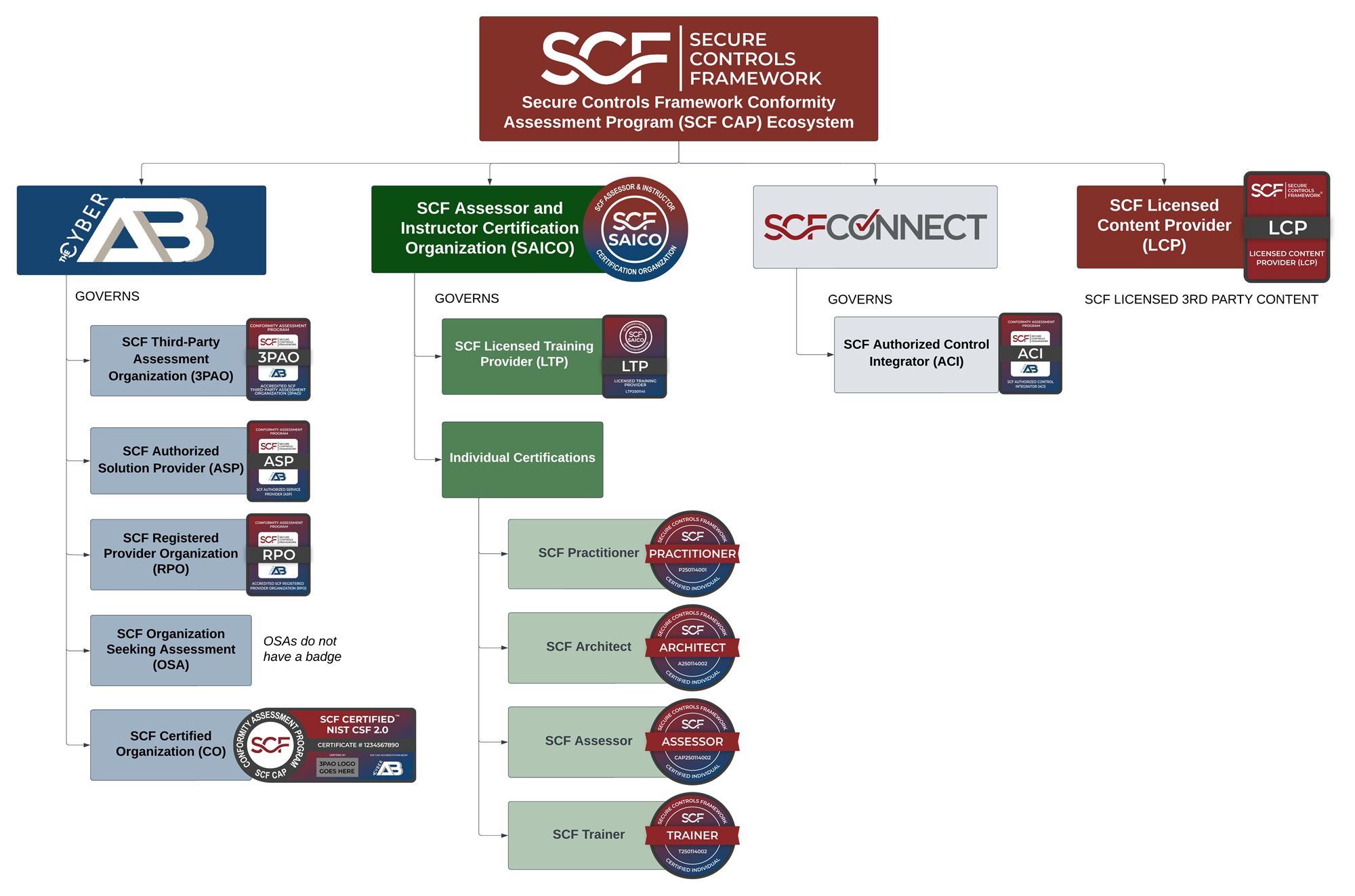
There are several key players in the SCF CAP Ecosystem that together form a complete, governed conformity assessment infrastructure.
Conformity assessment bodies accredited by The Cyber AB that perform 3PAAC Services. They conduct assessments, produce the ROC, and authorize certification issuance.
Consulting and advisory organizations registered to provide SCF implementation, advisory, and SCF CAP preparation services to OSAs.
The organization pursuing SCF CAP certification. Defines its assessment boundary, prepares evidence, and undergoes the two-phase process.
Organizations authorized to provide technology solutions that integrate with or support the SCF CAP assessment process and evidence collection.
Organizations authorized to integrate SCF controls into products and services, providing pre-mapped control evidence enabling inheritance and reciprocity.
Organizations licensed to incorporate SCF content into their commercial products, tools, and platforms under the SCF licensing program.
The SCF CAP requires clear assessment boundary demarcation using the People, Processes, Technologies, Data, and Facilities (PPTDF) model. The Unified Scoping Guide (USG) provides the methodology for defining what is in scope.
Distinguishes between Minimum Compliance Requirements (MCR), which are mandatory controls driven by obligations, and Discretionary Security Requirements (DSR), which are voluntary controls based on industry practices and risk tolerance.
Supports control inheritance (receiving protection from other entities’ controls) and reciprocity (accepting each other’s assessments). Documented through First-Party Declarations (1PD) and Third-Party Attestations (3PA).
Requires defining an SSOT and Systems of Record (SoR) to ensure assessment evidence is authoritative, traceable, and verifiable. The SSOT serves as the definitive reference for control implementation status.