Understanding GRC is the foundation of every effective cybersecurity and data privacy program. The Secure Controls Framework (SCF), the exclusive Common Controls Framework™ (CCF), provides the most comprehensive, free, and transparent GRC metaframework available, built by industry-leading volunteer experts.
GRC is an acronym for Governance, Risk, and Compliance, sometimes written as Governance, Risk Management and Compliance. It serves as the structured basis for an organization's cybersecurity and data protection practices.
The inside joke in the industry is that GRC also stands for “General Reading & Comprehension”, because one of the most persistent challenges in cybersecurity is professionals failing to thoroughly read the requirements they are tasked with implementing.
At its core, GRC provides the organizational framework to define, implement, measure, and continuously improve cybersecurity controls. The SCF, as the Common Controls Framework™, provides the most comprehensive GRC control catalog freely available, serving as the bridge between all major laws, regulations, and frameworks through a single integrated control set.
What are controls?
A control is power to influence or direct behaviors and events. Controls are your cybersecurity and data privacy program, and they define what must be done, who is responsible, and how it is verified. They form the operational backbone of every compliant and secure organization.
A central debate among GRC professionals: does Governance, Risk, or Compliance come first? The SCF provides a clear answer grounded in operational reality.
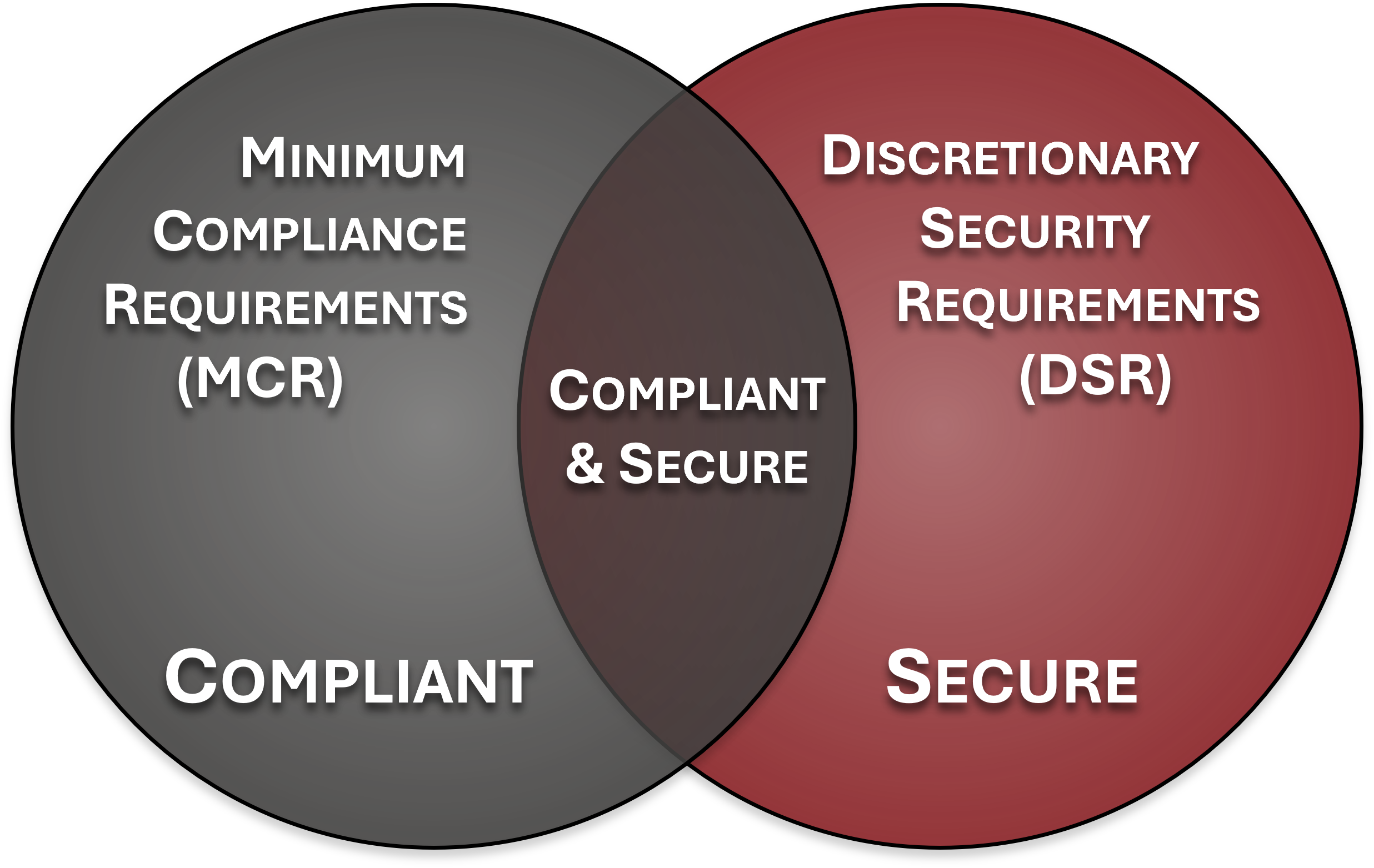
Compliance is the logical starting point. It is a fact-finding exercise to identify what statutory, regulatory, and contractual obligations apply to your organization. This defines the non-negotiable baseline: Minimum Compliance Requirements (MCR). MCR = External Obligations.
Once MCR and Discretionary Security Requirements (DSR) are defined, Governance operationalizes them through policies, standards, and SOPs. Governance assigns ownership via RASCI and ensures controls are built into administrative, technical, and physical requirements. DSR = Internal Risk Decisions.
Risk Management is ongoing throughout the GRC lifecycle, weighing controls, maintaining the risk register, performing assessments, and translating compliance and governance activities into an organization's current risk posture. It defines acceptable and unacceptable risk thresholds. Continuous PDCA Lifecycle.
.png)
The Three-Legged Stool Principle
In an ongoing GRC program, all three functions interact continuously in a "three-legged stool" approach with equal strength and importance for each function. Removing or weakening any leg causes the program to collapse. The SCF's Integrated Controls Management (ICM) model ensures all three legs remain equally strong through the continuous Plan-Do-Check-Act (PDCA) cycle.
The fact-finding function. Identifies every applicable statutory, regulatory, and contractual obligation the organization must satisfy. Responsibilities include:
The operationalization function. Develops policies and standards, assigns control ownership, and drives due diligence documentation. Responsibilities include:
The continuous assessment function. Maintains the risk register, weights controls, performs assessments, and enforces risk tolerance. Responsibilities include:
Understanding the difference between Minimum Compliance Requirements and Discretionary Security Requirements is critical to building a mature GRC program. Compliant ≠ Secure.
Controls that represent the minimum bar required by external obligations such as laws, regulations, and contracts. These are non-negotiable. Not implementing them creates legal or contractual exposure.
Controls selected based on the organization's own risk appetite and judgment. These go beyond the minimum and represent best-practice enhancements driven by internal risk management.
Why This Distinction Matters for Risk Management
Without clearly defining MCR and DSR thresholds, an organization’s cybersecurity program lacks anchoring to clear requirements. Clarifying the difference between “compliant” (MCR) and “secure” (MCR + DSR) is what elevates risk management discussions from checkbox compliance to genuine risk reduction. The SCF as the Common Controls Framework™ maps every MCR and DSR to specific controls across all 33 domains.
The SCRMS is a holistic, technology-agnostic approach to cybersecurity and data protection controls. It is designed to help organizations identify, implement and manage Secure, Compliant and Resilient (SCR) capabilities covering People, Processes, Technologies, Data & Facilities (PPTDF).
By design, the SCRMS expands upon and modernizes the concept of traditional Information Security Management System (ISMS) models, due to the archaic nature of multiple, siloed “management systems.” The use of siloed ISMS, AIMS and similar stand-alone management systems fails to address the reality of modern business practices. The SCRMS offers a broader “security, compliance and resilience ecosystem” mindset designed to provide necessary coverage for applicable risks and threats.
The SCRMS is focused on “defensible governance” to ensure due diligence and due care exists for decision-making, ownership and oversight of controls. The underlying expectation is for those charged with developing, implementing and governing security, compliance and resilience capabilities to do so in a reasonable manner that would withstand external scrutiny from regulators, class action lawsuits, insurers and other parties. The SCRMS comes with a companion document, the SCRMS Prioritized Implementation Guide (SCRMS-PIG), that provides a “paint by numbers” approach to implementing the SCF.
Framework-agnostic, enabling alignment with one or more laws, regulations and/or frameworks simultaneously
SCRMS-PIG companion guide provides a prioritized, “paint by numbers” approach to implementing the SCF
Covers People, Processes, Technologies, Data & Facilities (PPTDF) regardless of how or where data is stored, processed or transmitted
Focused on "defensible governance," producing evidence that withstands external scrutiny from regulators, lawsuits and insurers
Addresses both internal controls and broader Cybersecurity Supply Chain Risk Management (C-SCRM)
Two Goals of the SCRMS
How GRC functions produce cybersecurity assurance, including what due diligence and due care evidence looks like, and how it supports audit and legal defensibility.
How to define what is material to your cybersecurity program, including which risks, controls, and incidents rise to the level of requiring board-level attention and SEC disclosure.
The critical distinctions between legally enforceable laws, binding regulations, and voluntary frameworks, and how each interacts with your compliance obligations.
Common GRC terminology misuses: Policy vs Standard vs Procedure, Risk vs Threat, Strategy vs Tactics, and Inheritance vs Reciprocity, all clarified.
TPRM & SCRM, integrity requirements, organizational resilience, and the ongoing MSP/MSSP accountability landscape, what’s shaping GRC programs today.
The complete Secure Controls Framework: 1,400+ controls, 200+ mappings, all 33 domains. Free forever under Creative Commons. No registration required.
The SCF, the Common Controls Framework™, is uniquely positioned as the world's most comprehensive, transparent, and freely available GRC control catalog.
The SCF holds exclusive trademark rights to the Common Controls Framework™ designation. Domains common-controls-framework.com and commoncontrolsframework.com both resolve to the SCF.
As a Living Control Set, the SCF is continuously updated by volunteer industry-leading cybersecurity and GRC experts. It is never stale, never static, and always current with the latest regulatory and threat landscape.
The SCF uses Set Theory Relationship Mapping (STRM) per NIST IR 8477 to validate all framework mappings. This provides unprecedented transparency and trust in how the SCF relates to other standards.
Used by leading GRC platforms worldwide. Importable as .csv or NIST OSCAL-compliant JSON, enabling seamless integration into any GRC tooling ecosystem.
A single SCF control implementation satisfies requirements across 200+ laws, regulations, and frameworks simultaneously. This is the ultimate control economy for compliance-driven organizations.
Volunteer-driven by industry-leading experts and released under Creative Commons licensing. No cost. No registration. No vendor lock-in. Pure community value.