Cybersecurity is a cost center, not a revenue-generating business function. That means cybersecurity competes with all other departments for budget, and it necessitates a compelling business case to justify needed technology and staffing. To present cybersecurity in the best light possible, it requires business planning, and with that comes a need to understand the components involved in planning.
Having a hierarchical business plan is a logical step to operationalize the business’ requirements. Understanding the hierarchy of business planning documentation can lead to well-informed risk decisions, which influences technology purchases, staffing resources, and management involvement.
This is your opportunity to step up by designing and implementing a cohesive cybersecurity strategy that will be an asset to your company and enable you to be the cybersecurity leader that your organization needs you to be.
Business leaders are getting smarter on the topic of cybersecurity, so cybersecurity leadership needs to rise above the Fear, Uncertainty & Doubt (FUD) mentality and deliver value that is commensurate with the needs of the business.
The Most-Abused Business Planning Terms
Some of the most-abused business planning statements are strategy, operations, and tactics. While these terms are used by organizations across the globe, the terms have their origins in military planning where the terms have very unique scopes that are important to understand.
The definitions of “strategy vs operations vs tactics” primarily come down to doctrine. The concepts of strategy, operations and tactics are directly rooted in military planning.
At the strategic level, an organization employs available resources to secure its business goals & objectives (e.g., corporate business plan). Strategy is the highest level of planning. It defines the destination and the overall approach for reaching it. In cybersecurity, a strategic plan answers: what are we trying to achieve, and why, over a multi-year horizon?
At the operational level, an organization uses available resources to attain those strategic goals & objectives within a specific Line of Business (LOB). Operations translate strategy into specific initiatives, programs, and resource allocations. In cybersecurity, an operational plan answers: what programs, tools, and teams will we put in place to execute the strategy?
At the tactical level, departments and teams employ techniques and procedures to support operational objectives, as defined by the Line of Business (LOB). Tactics are the day-to-day activities, controls, and procedures that implement the operational plan. In cybersecurity, a tactical plan answers: what specific steps will individuals and teams take today, this sprint, or this quarter?
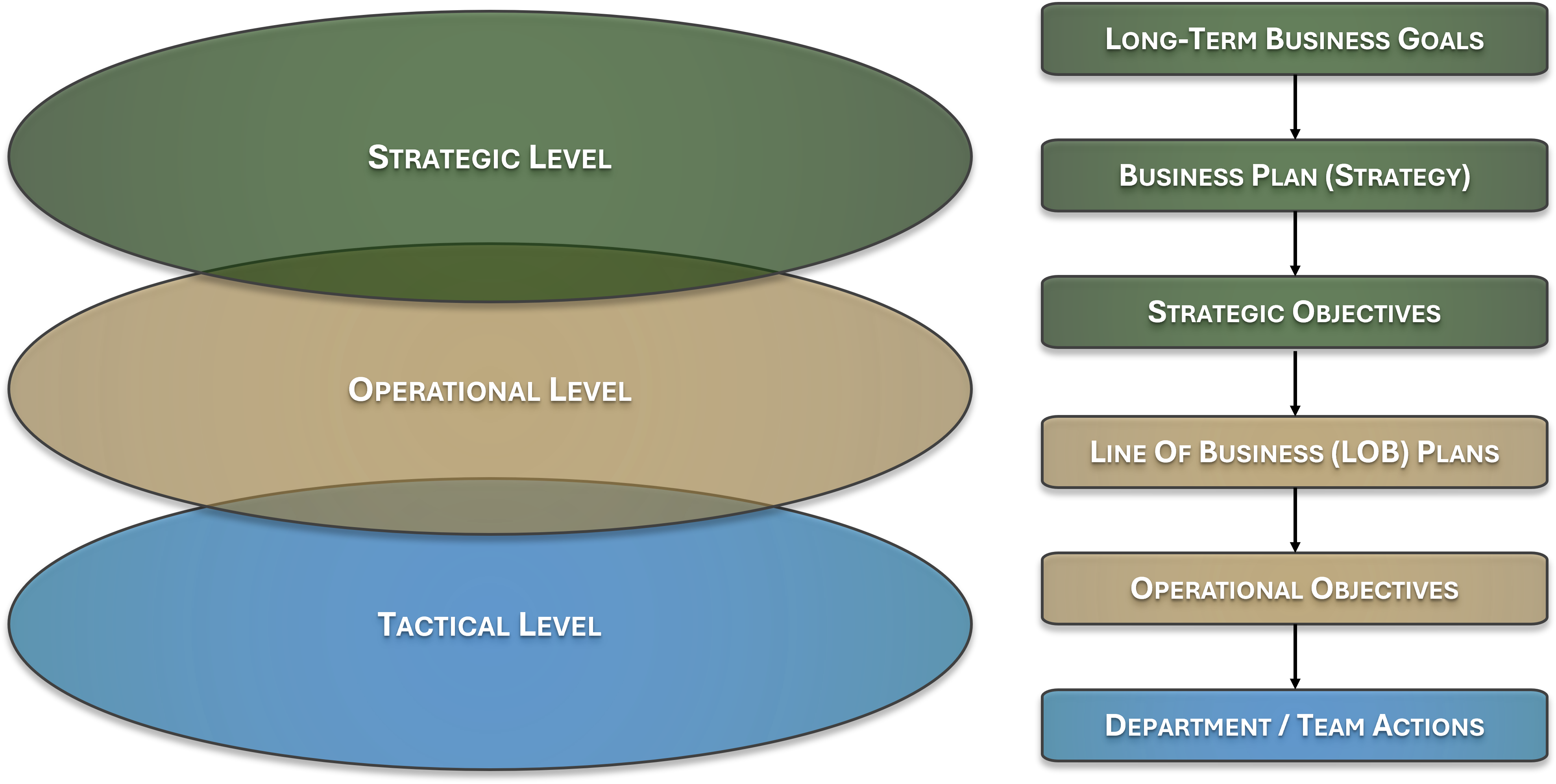
US Army Field Manual (FM) 100-5, 1982: The US Army's formalization of this doctrine occurred in the 1982 release of Field Manual (FM) 100-5 as a way to formalize a logical approach to describe the “levels of war” that span from the generals in charge, all the way to the lowly private in the trenches. There is overlap between strategic, operational and tactical levels, so there is no clear demarcation that can be uniformly applied to all organizations. The actions of individual contributors at the tactical level stack up to support broader operational goals, which in turn are designed to support a strategy that is aligned with the company’s success.
Understanding where you operate in this hierarchy, and communicating at the right level to the right audience, is what separates cybersecurity leaders from cybersecurity technicians.
A board or CEO operates at the strategic level. They need to know whether the organization’s cybersecurity strategy is aligned with the business plan, whether adequate resources are committed, and whether the risk posture is acceptable. They do not need patch counts or vulnerability scanner output.
A department head or program manager operates at the operational level. They need to understand which initiatives are funded, which programs are in-flight, and whether the team has the resources to deliver against the strategic goals.
A security engineer or analyst operates at the tactical level. They need clear procedures, defined tools, and specific objectives to execute against. Presenting strategic vision to a team of tacticians without operational context leaves them with no actionable guidance.
The Common Mistake
Cybersecurity teams routinely conflate these levels, presenting tactical details to strategic audiences (the board does not need to hear about CVE counts), or presenting strategic vision to tactical teams without translating it into actionable operational programs. Knowing your audience and their level of the hierarchy is the starting point for every effective cybersecurity communication.
An organization employs available resources to secure its business goals & objectives (e.g., corporate business plan). Audience: CEO, Board, Executive Leadership.
An organization uses available resources to attain those strategic goals & objectives within a specific Line of Business (LOB). Audience: Department Heads, Program Managers, CISOs.
Departments and teams employ techniques and procedures to support operational objectives, as defined by the LOB. Audience: Security Engineers, Analysts, Administrators, Individual Contributors.