The Unified Scoping Guide (USG) is a free resource that helps organizations define the scope of sensitive and regulated data where it is processed, stored and/or transmitted. Using a zone-based model with nine zones, the USG categorizes system components to determine what falls in and out of scope for cybersecurity and data protection requirements.
The USG is intended to help organizations define the scope of sensitive and/or regulated data where it is Processed, Stored and/or Transmitted (P/S/T). The guide categorizes system components according to several factors: whether sensitive data is being stored, processed, or transmitted; the functionality that the system component provides; and the connectivity between the system and the Sensitive Data Environment (SDE).
In practical terms, cybersecurity and data protection controls exist to protect an organization’s data. Assets such as laptops, servers, and network infrastructure are commodities that can be easily replaced, but data residing on those devices cannot. This concept of being data-centric is crucial when developing, implementing, and governing a cybersecurity and data protection program.
The SDE encompasses the People, Processes, Technologies, Data & Facilities (PPTDF) that process, store and/or transmit sensitive and regulated data.
Scoping ≠ Applicability
The USG does not define which statutory, regulatory, or contractual controls are required for each category. Scoping defines the boundary; applicability defines the controls within that boundary. Each organization and its assessor must determine the nature, extent, and effectiveness of each control.
The USG’s data-centric security approach is applicable to a wide range of sensitive and regulated data types. The guide refers to both sensitive and regulated data as “sensitive data” to simplify the scoping concept.
Government-controlled information requiring safeguarding per NIST SP 800-171, CMMC, and 32 CFR Part 170. The USG includes specific CMMC scoping guidance with asset categorizations aligned to DoD requirements.
Personal data as defined by US federal (OMB, NARA), state government, and European Union (GDPR) regulations. Includes any information that can be used to identify, contact, or locate an individual.
Payment card data governed by PCI DSS requirements. The USG leverages PCI DSS scoping concepts and extends them to other data types using the same zone-based methodology.
Health information governed by HIPAA/HITECH requirements. Includes individually identifiable health information transmitted or maintained in any form or medium.
Information provided by or generated for the US Government under contract, not intended for public release. Subject to CMMC Level 1 requirements.
Proprietary information including trade secrets, proprietary algorithms, product designs, and business-critical data that provides competitive advantage.
Legally privileged communications between an organization and its legal counsel. Requires specific handling and access controls to maintain privilege.
Data controlled under the International Traffic in Arms Regulations (ITAR) or Export Administration Regulations (EAR). Subject to strict access and transmission controls.
Educational records governed by the Family Educational Rights and Privacy Act. Includes personally identifiable information from education records.
Information related to critical infrastructure systems whose compromise could have a debilitating impact on security, economic stability, or public health and safety.
The USG utilizes nine zones to categorize system components based on their interaction with sensitive and regulated data. Each zone has a different risk profile and different scoping implications.
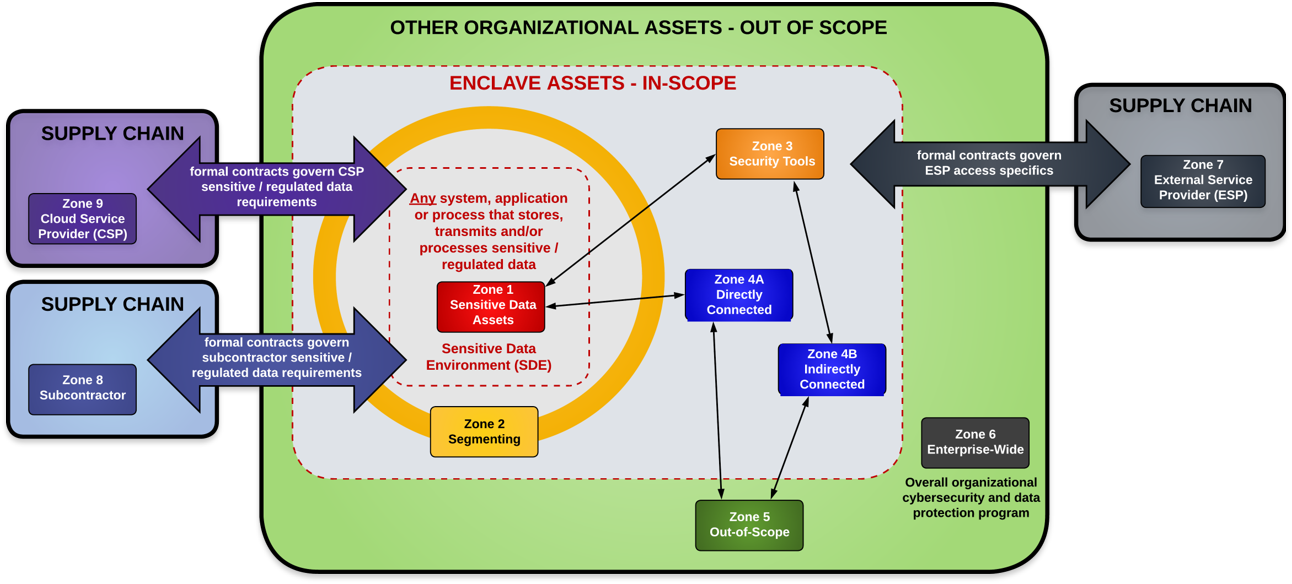
The USG defines two levels of scoping: macro scoping to define the overall assessment boundary, and micro scoping to define control applicability within that boundary using the PPTDF framework.
Assessment Boundary (Macro Scoping): Macro scoping defines the overall organizational boundary for the assessment. This may be the entire organization, a specific contract or project, a specific business unit, or a specific geographic region of operations.
Control Applicability (Micro Scoping with PPTDF): Within the assessment boundary, micro scoping uses the PPTDF framework to determine where controls apply across three categories:
Administrative: People-centric and process-centric controls, including policies, standards, procedures, training, roles, and responsibilities.
Physical: Facility-centric controls, including physical access, environmental protections, media handling, and physical security of data centers and work areas.
Technical: Technology-centric and data-centric controls, including access controls, encryption, logging, monitoring, network segmentation, and system configurations.
The USG includes six worked example scenarios showing how to apply the zone-based model to real-world network architectures, from flat networks to hybrid cloud environments.
CUI resides on a flat, unsegmented network. All systems are in scope because there is no segmentation boundary. Demonstrates why flat networks maximize scope and cost.
CUI is isolated to a segmented portion of the network using firewalls and VLANs. Demonstrates how segmentation reduces the scope to only those systems within and protecting the CUI boundary.
CUI resides entirely in cloud infrastructure. Demonstrates CSP shared responsibility and how Zone 9 (Cloud Service Provider) applies alongside the organization’s own controls.
CUI spans both on-premise and cloud infrastructure. Demonstrates the most complex scoping scenario with multiple zone interactions and shared responsibility across environments.
Non-CUI sensitive data (intellectual property and personal data) on a flat network. Demonstrates that the USG applies beyond government data to commercial sensitive data types.
Commercial sensitive data isolated through segmentation. Shows how organizations can reduce scope for PII, IP, and other non-government data using the same zone-based approach.
The USG defines the assessment boundary, which is the starting point for every SCF tool in the assessment ecosystem. Without proper scoping, no assessment is reliable.
CDPAS Standard 3.2 (Assessment Boundary Demarcation) and Standard 3.3 (Graphical Representation) use the USG to define what is in scope. The USG output is the direct input to CDPAS scope definition.
The ERL defines what evidence must be collected for each in-scope control. The USG determines which controls are in scope; the ERL operationalizes the evidence collection within that boundary.
The SCR-RMM Step 9 (Establish Context) uses the USG to establish the organizational and environmental context for assessing risks. Scoping defines where risk management activities focus.
Maturity scoring only applies to in-scope controls. The USG determines the scope; the SCR-CMM provides the maturity measurement for controls within that scope.
The SCF’s 1,400+ controls provide the control applicability once scoping is defined. The USG determines the boundary; the SCF catalog provides the controls that apply within each zone.
The USG defines the assessment boundary for SCF-CAP conformity assessments. Without a properly defined scope, no conformity certification is meaningful.
The USG includes additional guidance on modern security architectures and data protection scenarios that affect scoping decisions.
Zero Trust Architecture (ZTA) Scoping: Guidance for scoping in Zero Trust environments, including DoD Zero Trust Overlays and DHS CISA Zero Trust Capability Framework (ZTCF) considerations.
Segmentation Considerations: How network segmentation affects zone boundaries and scope reduction. Properly implemented segmentation is the primary mechanism for reducing assessment scope and cost.
Data Spillage Prevention & Response: Guidance on viewing scoping from a data spillage perspective, including what happens when sensitive data ends up where it shouldn't and how to respond.
VDI Scoping Considerations: Specific guidance for Virtual Desktop Infrastructure environments and how VDI architectures affect zone categorization.
Data Flow Diagrams (DFD): Examples of how to create data flow diagrams that support scoping exercises, including CUI data flow diagram examples.
Appendices & Supporting Materials
The USG includes appendices covering: example data flow diagrams, VDI scoping considerations, defining “must have” vs “nice to have” controls, and documentation to support cybersecurity and data protection programs.