In GRC operations, words have specific meanings. The concept of risks vs threats is a common “word crimes” incident. These terms are not interchangeable, and confusing them leads to risk registers that cannot be acted on and boards that cannot make informed decisions.
The following terms are commonly confused or conflated in GRC operations. Each has a distinct, authoritative meaning that determines how it is used in policies, risk registers, control frameworks, and audit contexts.
A person or thing likely to cause damage or danger (noun) or to indicate impending damage or danger (verb).
A situation where someone or something valued is exposed to danger, harm or loss (noun) or to expose someone or something valued to danger, harm or loss (verb).
A weakness in an information system, system security procedures, internal controls, or implementation that could be exploited or triggered by a threat source.
The safeguards or countermeasures prescribed for an information system or an organization to protect the confidentiality, integrity, and availability of the system and its information.
The security controls employed in lieu of the recommended control(s) that provide equivalent or comparable protection for an information system or organization.
A set of instructions used to describe a process or procedure that performs an explicit operation or explicit reaction to a given event. The design and implementation of a procedure must be reasonable and appropriate to address the control.
Appropriate or fair level of care. This forms the basis of the legal concepts of “due diligence” and “due care” that pertain to negligence.
To make less severe or painful or to cause to become less harsh or hostile.
These terms do not exist in isolation. They form an interconnected ecosystem. Understanding how they relate is fundamental to building a risk management program that can survive regulatory scrutiny.
The Risk Ecosystem Flow
A threat (ransomware operator) exploits a vulnerability (unpatched system) to cause a risk (data encryption with $X impact at Y% likelihood). A control (patch management + network segmentation) reduces that risk. A compensating control is used where a primary control cannot be applied. A procedure documents how the control is operationalized. The whole system is governed by the standard of reasonable care, and the organization mitigates risk through this layered approach.
Threats represent a person or thing likely to cause damage or danger. Natural and man-made threats affect control execution (e.g., if the threat materializes, will the control function as expected?). Threats exist in the natural world that can be localized, regional or worldwide (e.g., tornados, earthquakes, solar flares, etc.). Threats can also be manmade (e.g., hacking, riots, theft, terrorism, war, etc.).
Anything (e.g., object, substance, human) that is capable of acting against an asset in a manner that can result in harm.
A potential cause of an unwanted incident.
Any circumstance or event with the potential to adversely impact organizational operations (including mission, functions, image, or reputation), organizational assets, or individuals through an information system via unauthorized access, destruction, disclosure, modification of information, and/or denial of service.
Risk represents a potential exposure to danger, harm or loss. Risk is associated with a control deficiency (e.g., if the control fails, what risk(s) is the organization exposed to?). Risk is often calculated by a formula of Threat × Vulnerability × Consequence in an attempt to quantify the potential magnitude of a risk instance occurring. While it is not possible to have a totally risk-free environment, it may be possible to manage risks by avoiding, reducing, transferring, or accepting the risks.
The combination of the probability of an event and its consequence.
The level of impact on organizational operations (including mission, functions, image, or reputation), organizational assets, individuals, other organizations, or the Nation resulting from the operation of an information system given the potential impact of a threat and the likelihood of that threat occurring.
A measure of the extent to which an entity is threatened by a potential circumstance or event, and typically is a function of: the adverse impact, or magnitude of harm, that would arise if the circumstance or event occurs; and the likelihood of occurrence.
A vulnerability is a weakness in an information system, system security procedures, internal controls, or implementation that could be exploited or triggered by a threat source. Vulnerabilities are distinct from risks. A vulnerability is a weakness, not an outcome. The exploitation of a vulnerability by a threat, resulting in impact, is what constitutes a risk.
Weakness in an information system, system security procedures, internal controls, or implementation that could be exploited or triggered by a threat source.
Controls are technical, administrative or physical safeguards. Controls are the nexus used to manage risks through preventing, detecting or lessening the ability of a particular threat from negatively impacting business processes. Controls directly map to standards, since control testing is designed to measure specific aspects of how standards are actually implemented.
The means of managing risk, including policies, procedures, guidelines, practices or organizational structures, which can be of an administrative, technical, management, or legal nature.
The policies, procedures, practices and organizational structures designed to provide reasonable assurance that business objectives will be achieved and undesired events will be prevented or detected and corrected. Measure that is modifying risk.
The safeguards or countermeasures prescribed for an information system or an organization to protect the confidentiality, integrity, and availability of the system and its information. The administrative, technical, and physical safeguards employed within an agency to ensure compliance with applicable privacy requirements and manage privacy risks.
The security controls employed in lieu of the recommended control(s) that provide equivalent or comparable protection for an information system or organization. Compensating controls are used when a primary control cannot be implemented due to a legitimate business reason or technical limitation. They are intended to reduce the increased risk created by the absence of the primary control.
Management, operational, and technical controls (i.e., safeguards or countermeasures) employed by an organization in lieu of the recommended controls in the security control baselines that provide equivalent or comparable protection for an information system or organization.
A set of instructions used to describe a process or procedure that performs an explicit operation or explicit reaction to a given event. The design and implementation of a procedure must be reasonable and appropriate to address the control. Procedures help address the question of how the organization actually operationalizes a policy, standard or control.
A document containing a detailed description of the steps necessary to perform specific operations in conformance with applicable standards. Procedures are defined as part of processes.
A set of instructions used to describe a process or procedure that performs an explicit operation or explicit reaction to a given event.
Appropriate or fair level of care. This forms the basis of the legal concepts of “due diligence” and “due care” that pertain to negligence. In cybersecurity and privacy law, “reasonable security” is not a fixed standard. It is evaluated by comparing an organization’s practices against what a reasonable organization in its position would have implemented, measured against published frameworks and industry standards.
The FTC, state attorneys general, and civil plaintiffs evaluate “reasonable security” based on the organization’s size, the sensitivity of data handled, the availability of known controls, and whether the organization followed published guidance from NIST, ISO or sector-specific regulators. Claiming practices were “reasonable” without documentary evidence of those practices is not a defense.
To make less severe or painful or to cause to become less harsh or hostile. In risk management, mitigation refers to control actions that reduce either the likelihood that a threat will successfully exploit a vulnerability, or the impact if it does. Mitigation is one of four common risk treatment options, alongside avoidance, transfer, and acceptance.
A mitigating control reduces risk but does not eliminate it. The residual risk remaining after mitigation must still be evaluated and either accepted, transferred (e.g., via insurance), or further mitigated. Risk registers must track both inherent risk and residual risk after controls are applied.
The relationship between these terms forms a predictable chain. Threats exploit vulnerabilities. Vulnerabilities, when exploited, create risks. Controls reduce those risks. Incidents occur when controls fail or are absent. Understanding this chain is what enables prioritized, defensible risk management decisions.
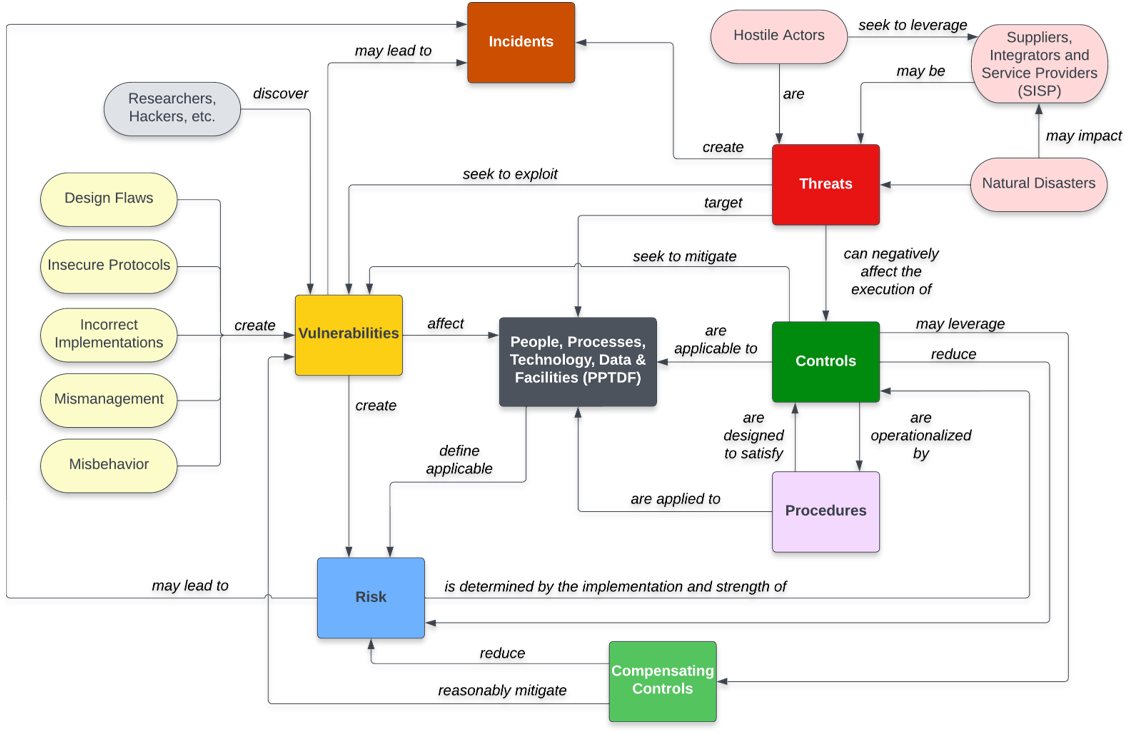
The Risk Ecosystem Flow
A threat (ransomware operator) exploits a vulnerability (unpatched system) to cause a risk (data encryption with $X impact at Y% likelihood). A control (patch management + network segmentation) reduces that risk. A compensating control is used where a primary control cannot be applied. A procedure documents how the control is operationalized. The whole system is governed by the standard of reasonable care, and the organization mitigates risk through this layered approach.