The Security, Compliance & Resilience Management System (SCRMS) will be published next week -sign up for the SCF Newsletter (bottom of the page) to be alerted to its launch.
Security, Compliance & Resilience Management System (SCRMS)
The Secure Controls Framework (SCF) Security, Compliance & Resilience Management System (SCRMS) is intended to be utilized as a holistic, technology-agnostic framework for an entity to design, implement and maintain secure, compliant and resilient capabilities, covering an organization’s People, Processes, Technology, Data and Facilities (PPTDF), regardless of how or where data is stored, processed and/or transmitted.
A Holistic, Technology-Agnostic Approach to Design, Implement and Maintain Secure, Compliant and Resilient Capabilities
The SCRMS is not a “one-size-fits-all” playbook, since the information in this document is meant to be adopted and tailored to the unique size, resources and risk circumstances of the entity. The SCRMS is:
- Framework-agnostic, allowing entities to leverage one or more frameworks that it needs to align with (e.g., NIST CSF 2.0, SOC 2, NIST 800-171, ISO 27001, etc.);
- Focused on supporting processes and practices that must exist for a cybersecurity and data protection program to operate effectively and efficiently;
- Designed to proactively address the strategic, operational and tactical nature of operating an entity’s cybersecurity and data protection program; and
- Designed to address both internal controls, as well as the broader concept of Cybersecurity Supply Chain Risk Management (C-SCRM).
 |
 |
By design, the SCRMS expands upon and modernizes the concept of traditional Information Security Management System (ISMS) models, due to the archaic nature of multiple, siloed “management systems” that are necessary to provide reasonable governance practices (e.g., Artificial Intelligence Management System (AIMS) add-on). The use of siloed ISMS, AIMS and similar stand-alone management systems fails to address the reality of modern business practices, since it is overly leveraged for marketing purposes. This does not serve assurance needs to demonstrate security, compliance or resilience that entities require. The SCRMS offers a broader “security, compliance and resilience ecosystem” mindset that is designed to provide the necessary coverage to address applicable risks and threats that entities face.
The SCRMS enables an entity to align with one, or more, laws, regulations and/or frameworks. For example, an entity that aligns with NIST CSF 2.0, but also has obligations for PCI DSS, ISO 27001, ISO 42001, HIPAA Security Rule and SOC 2 can leverage a “living control set” that is capable of adjusting to the specific security, compliance and resilience requirements it must address.
Security, Compliance & Resilience Management System (SCRMS) Goals
There are two (2) fundamental goals of the Security, Compliance & Resilience Management System (SCRMS):
- Provide the structure for an entity to be secure, compliant and resilient; and
- Generate defensible evidence of due diligence and due care that is capable of defending the entity’s cybersecurity and data protection practices to against legal challenges, if an incident should occur.
CISO's need to be able to speak in a language that executives will understand. This includes being able to defend against claims of negligence that can be uncovered through external scrutiny (e.g., class action lawsuits, regulators, insurers, etc.). This is a very real threat, regardless of the industry, requiring the CISO to frame current and targeted capabilities in the context of how it helps an entity be secure, compliant and resilient, while supporting the broader mission and business functions.
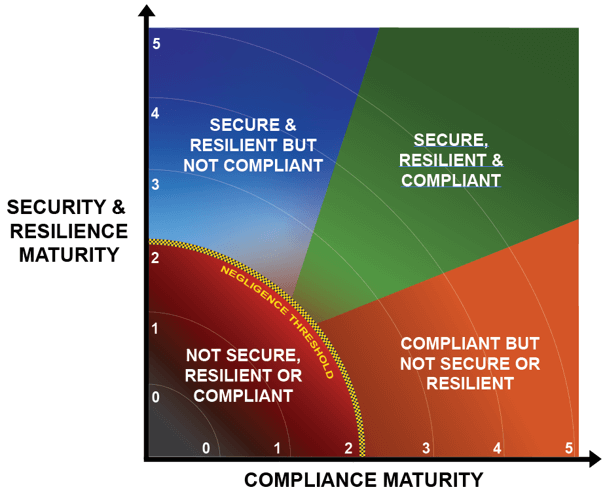
An entity’s status can be visualized as being in one (1) of four (4) maturity-based quadrants. When you look at the image below, which quadrant do you want to be in? Even more important, which quadrant can you prove you are in with available evidence you have on hand?
- Not secure, compliant or resilient (negligent);
- Secure & resilient, but not compliant;
- Compliant, but not secure or resilient; or
- Secure, compliant & resilient.
Can your executive leadership withstand external scrutiny when answering these questions:
- Who owns and accepted key risks?
- When those decisions were last reviewed?
If not, your governance operating model is incomplete. The SCRMS can help close that gap.
The SCRMS Defines What It Means To Be Secure, Compliant & Resilient
Secure, compliant and resilient capabilities exist when applicable controls are properly scoped and implemented. The SCRMS specifically addresses the need to clarify the difference between "compliant" versus "secure" since that understanding is necessary to have coherent risk management discussions.
To assist in this process, an entity’s applicable controls are categorized according to “must have” vs “nice to have” requirements:
- Minimum Compliance Requirements (MCR) are the absolute minimum requirements that must be addressed to comply with applicable laws, regulations and contracts (e.g., mandatory requirements). MCR are primarily externally-influenced, based on industry, government, state and local regulations. MCR should never imply adequacy for secure practices and data protection, since they are merely compliance-related.
- Discretionary Security Requirements (DSR) are tied to the entity’s risk appetite since DSR are “above and beyond” MCR, where the entity self-identifies additional cybersecurity and data protection controls to address voluntary industry practices or internal requirements, such as findings from internal audits or risk assessments (e.g., discretionary requirements). DSR are primarily internally-influenced, based on the entity’s respective industry and risk tolerance. While MCR establish the foundational floor that must be adhered to, DSR are where entities often achieve improved efficiency, automation and enhanced security.
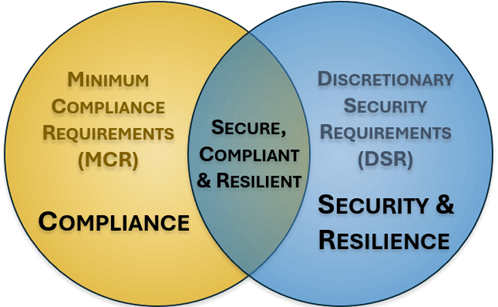
The combination of MCR and DSR equate to an entity’s Minimum Security Requirements (MSR), which define the “must have” and “nice to have” requirements in one control set. This control set defines the Minimum Viable Product (MVP) technical and business requirements from a cybersecurity and data protection perspective. The MSR can be considered to be an entity’s IT General Controls (ITGC), which establish the necessary controls that must be applied to applicable Technology Assets, Applications, Services and/or Data (TAASD).
Who Is The SCRMS For?
The SCRMS is written for senior cybersecurity practitioners and executives, specifically those in the following roles:
- Chief Information Security Officer (CISO); and
- Governance, Risk & Compliance (GRC) Director.
While any cybersecurity practitioner can benefit from the information provided in the SCRMS, those roles listed above are the primary decision-makers within an organization that enable a focus on secure, compliant and resilient practices. Their utilization of the SCRMS will trickle down to all other parts of the entity’s cybersecurity and data protection program.
What Does It Mean To Be Secure?
An entity can reasonably claim it is secure if it has implemented and operational defenses focused on Confidentiality, Integrity, Availability and Safety (CIAS). An entity’s level of security is dynamic, based on its:
- Implemented defensive capabilities; and
- Applicable risks and threats.
What Does It Mean To Be Compliant?
An entity can reasonably claim it is compliant if it has the ability to demonstrate conformity with applicable laws, regulations and other obligations. The scope of compliance includes both external and internal requirements.
What Does It Mean To Be Resilient?
An entity can reasonably claim it is resilient if it has prepared for and has the ability to adapt to changing conditions, where it can withstand and/or recover rapidly from disruption. Resilience includes the ability to withstand and recover from deliberate attacks, accidents or naturally occurring threats or incidents.
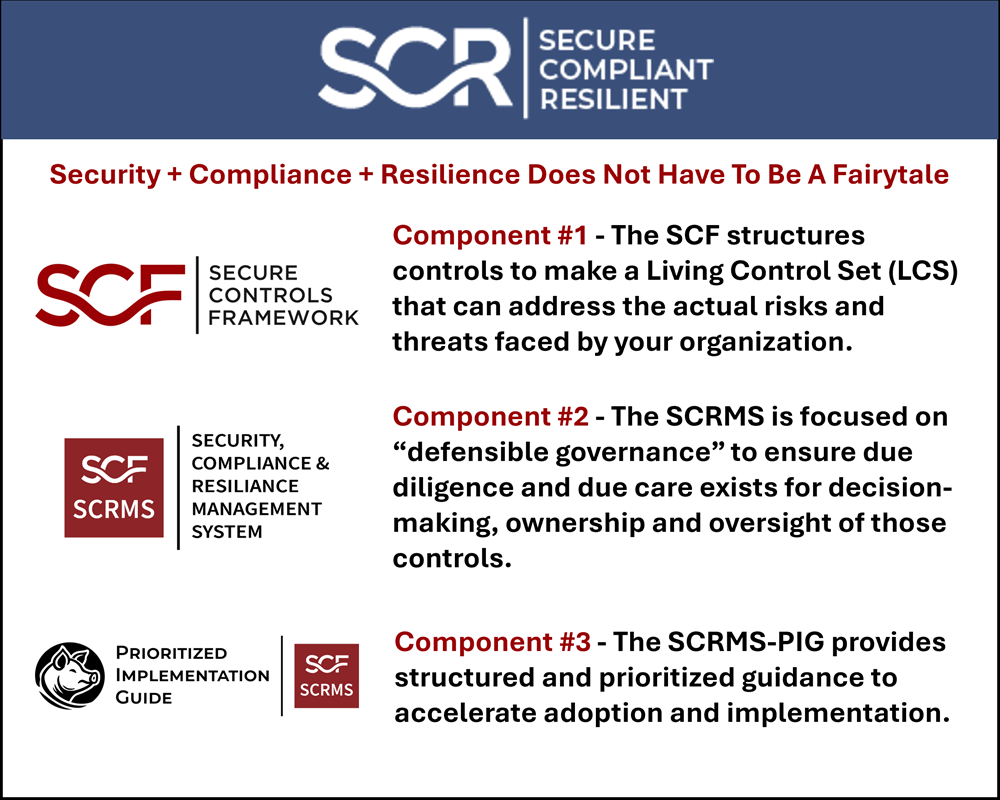
Component 1: Secure Controls Framework (SCF)
The SCF structures controls to make a Living Control Set (LCS) that can address the actual risks and threats faced by your organization. If you do not already have the SCF, download it for free from the SCF Download Page.
Component 2: Security, Compliance & Resilience Management System (SCRMS)
The SCRMS is focused on “defensible governance” to ensure due diligence and due care exists for decision-making, ownership and oversight of those controls. It is not a lightweight framework and that’s its value. With a focus on being secure, compliant & resilient, this is built for organizations that want to be:
SCRMS is not:
❌ A new compliance framework
❌ A replacement for NIST or ISO
❌ A tool or platform
SCRMS is:
✔ A way to make security decisions defensible
✔ A bridge between executives and practitioners
Component 3: The SCRMS-PIG Is A "How To GRC" Playbook - A Prioritized Implementation Guide
The Security, Compliance & Resilience Management System Prioritized Implementation Guide (SCRMS PIG) is the operational companion to the SCRMS. The SCRMS-PIG provides structured and prioritized guidance to accelerate adoption and implementation.
It provides a sequenced, dependency-aware roadmap for implementing SCRMS capabilities in a way that:
- Supports the entity’s mission and business practices;
- Avoids rework from implementing capabilities where dependencies exist that results in cascading failures from misaligned PPTDF;
- Aligns funding and resources with business risk;
- Avoids systemic weaknesses by building foundational capabilities before chasing advanced capabilities; and
- Provides assurance to stakeholders through audit-ready evidence.
The SCRMS is not about perfect security. It is about reasonable, defensible and governable security, compliance and resilience that is designed to withstand scrutiny and support the entity’s mission over time. The SCRMS-PIG makes that outcome achievable, measurable and sustainable.
The SCRMS-PIG breaks down control implementation into thirty (30) major steps, which can then be translated into a viable project plan.
- Twenty-six (26) steps are focused on due diligence activities; and
- Four (4) steps are focused on due care activities.
The structure of the SCRMS-PIG is designed to support:
- Strategic decision-making
- Budget justification for cybersecurity and data protection capabilities;
- Deficiency remediation; and
- Audit readiness is a byproduct of defensible governance
 |
 |
A Plan, Do, Check & Act Approach To Being Secure, Compliant & Resilient
The SCRMS takes a comprehensive view towards governing a cybersecurity & data privacy program. Without an overarching concept of operations for the broader GRC/IRM function, organizations will often find that their governance, risk, compliance and privacy teams are siloed in how they think and operate. These siloed functions and unclear roles often stem from a lack of a strategic understanding of how these specific functions come together to build a symbiotic working relationship between the individual teams that enables quality control over people, processes and technology.
The SCRMS utilizes a Plan, Do, Check & Act (PDCA) approach that is a logical way to design a governance structure:
|
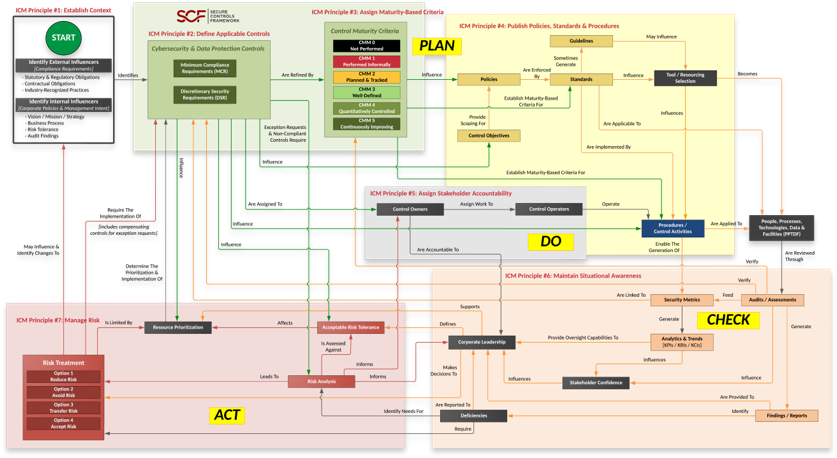 |
Security, Compliance & Resilience Management System (SCRMS) Principles
There are nine (9) principles associated with the SCRMS:
SCRMS Principle 1: Establish Context
To build and maintain efficient and effective operations, a cybersecurity and data protection program must have a hierarchical vision, mission and strategy that directly supports the entity’s broader strategic objectives and business processes. This process of establishing context involves identifying all applicable external compliance requirements (e.g., laws, regulations and contractual obligations), internal directives (e.g., Board of Directors, corporate policies, etc.). This also includes understanding applicable risks and threats, since the entity’s exposure to those may influence the need for controls beyond those that are mandated as compliance obligations.
Establishing context is both a due diligence and due care element of an entity’s cybersecurity and data protection program, since context changes with time. Things to consider when establishing context:
- Mission / vision / strategy of the entity;
- Statutory (law), regulatory (regulation) and contractual requirements for cybersecurity and data protection;
- Fiscal constraints;
- The entity’s structure;
- The entity’s risk profile (including risk appetite, risk tolerance and risk threshold considerations);
- Planned organizational changes (e.g., Mergers, Acquisitions & Divestitures (MA&D));
- Corporate culture (e.g., how receptive is the entity to change); and
- Geographic-specific requirements.
SCRMS Principle 2: Identify Applicable Controls
A tailored set of cybersecurity and data protection controls must exist for an entity to implement a SCRMS. This control set needs to be tailored for the entity’s unique requirements, such as a combination of Minimum Compliance Requirements (MCR) and Discretionary Security Requirements (DSR). This blend of “must have” and “nice to have” requirements establish an entity’s tailored control set to help ensure secure, compliant and resilient capabilities.
SCRMS Principle 3: Define Maturity Expectations
The entity must define maturity expectations for its cybersecurity and data protection controls. From the perspective of the SCRMS, the maturity expectations define entity-specific “what right looks like” expectations for control implementation and continued operation. The maturity-based criteria are applicable to People, Processes, Technologies, Data & Facilities (PPTDF).
Maturity targets are expected to directly support the entity’s need for security, compliance and resiliency capabilities. These maturity targets can be used by an entity’s leadership for:
- Multi-year business planning;
- Budgeting; and
- Assessment criteria.
SCRMS Principle 4: Publish Governance Documentation
Cybersecurity and data protection documentation must exist, otherwise an entity’s governance practices are both unenforceable and indefensible. Formalizing entity-specific requirements via documented policies, standards and procedures are necessary to operationalize cybersecurity and data protection controls.
Documented policies, standards and procedures provide evidence of due diligence that the entity identified and implemented reasonable steps to address its applicable requirements. The output of procedures provides evidence of due care that controls were operated as described.
SCRMS Principle 5: Assign Stakeholder Accountability
Controls must be assigned to stakeholders to ensure accountability (e.g., business units, teams and/or individuals). These “control owners” are expected to assign the task of executing controls to “control operators” at the Individual Contributors (IC)-level.
- Stakeholders utilize the prescriptive requirements from policies and standards to develop Standardized Operating Procedures (SOP) that enable ICs to execute those controls.
- The documented execution of procedures provides evidence of due care that reasonable practices are being performed.
SCRMS Principle 6: Prioritize Capabilities According To Risk
Security, compliance and resilience capabilities must be prioritized based on applicable risks and threats. Not all risks and threats are equal, so a risk-based prioritization must occur.
SCRMS Principle 7: Maintain Situational Awareness
Situational awareness must involve more than merely “monitoring controls” (e.g., metrics). While metrics are a point-in-time snapshot into discrete controls performance, the broader view of metrics leads to a longer-term trend analysis (e.g., analytics). When properly tied in with current audits, control deficiencies, risk, threat and vulnerability information, this broader insight provides “situational awareness” that is necessary for an entity’s leadership to adjust plans to operate within the defined risk threshold.
SCRMS Principle 8: Manage Risk
Proactive risk management processes must exist across all phases of Technology Assets, Applications, Services and/or Data (TAASD) life cycles to address Confidentiality, Integrity, Availability and Safety (CIAS) aspects. Based on finite resources (e.g., time, personnel and money), it is necessary to utilize prioritized risk management practices that ensure issues posing the highest risk are addressed first.
Risk management must address internal and external factors, including data privacy, Artificial Intelligence (AI), embedded technology and Supply Chain Risk Management (SCRM) considerations. To manage risk, it requires the entity to enforce a clearly-defined risk threshold and ensure reasonable security practices are operational.
SCRMS Principle 9: Evolve Processes
Cybersecurity and data protection measures must adapt and evolve to address business operations and the evolving threat landscape. This requires the adoption of a Plan, Do, Check & Act (PDCA) approach (e.g., Deming Cycle) to ensure the entity proactively identifies its requirements, implements appropriate protections, maintains situational awareness to detect incidents, operates a viable capability to respond to incidents and can sustain key business operations, if an incident occurs.
Things to consider when evolving processes:
- Changes in the compliance landscape (e.g., laws, regulations and contractual obligations);
- Technology changes; and
- Budget/resourcing constraints that affect how processes are implemented.
