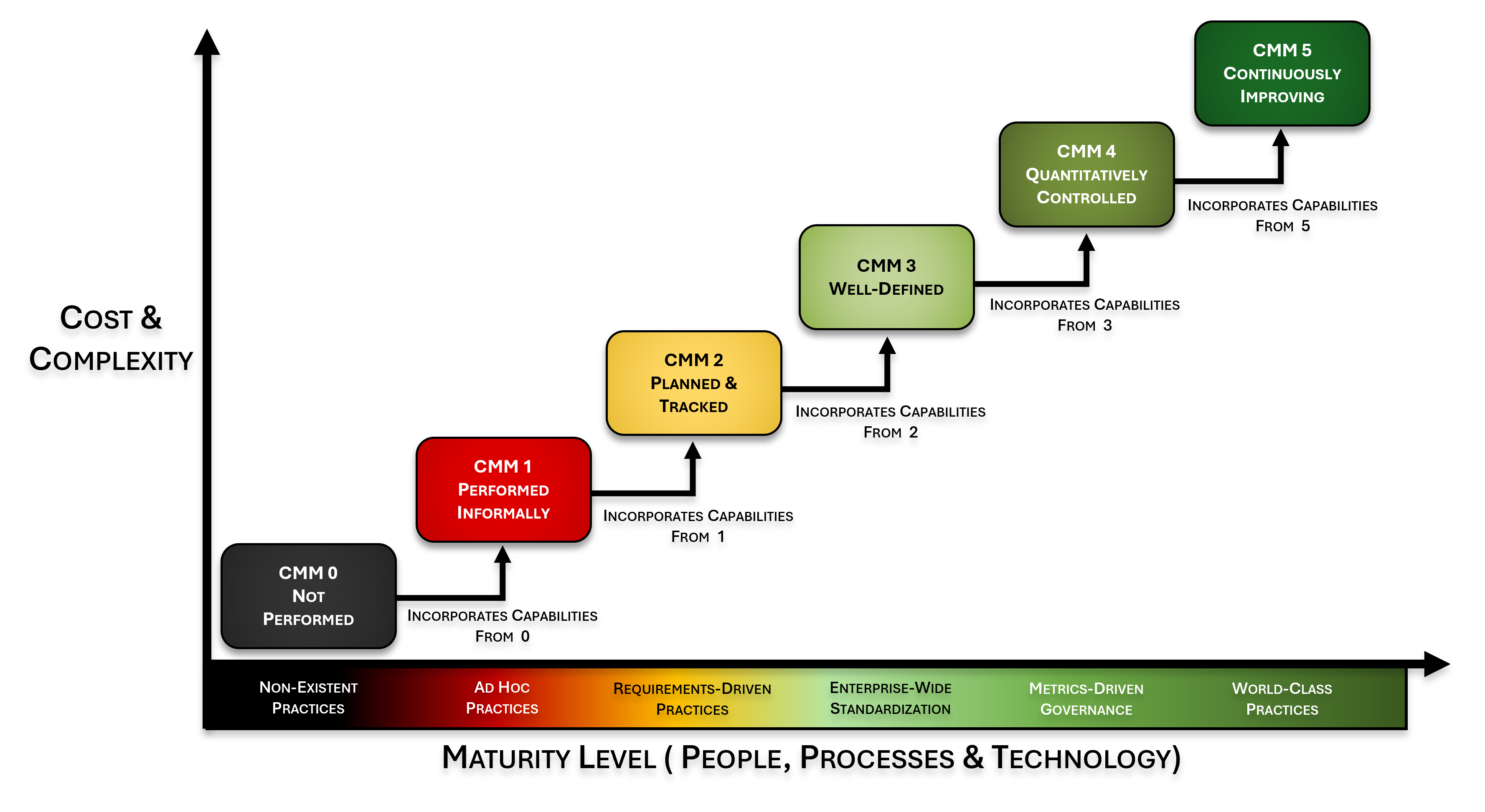
The Secure, Compliant & Resilient Capability Maturity Model (SCR-CMM) provides a six-level (L0–L5) maturity scoring system for every control in the Secure Controls Framework (SCF), enabling organizations to objectively assess where they are today, define where they need to be, and measure progress over time. Built on the SSE-CMM v2.0 structure.
The SCR-CMM is meant to solve the problem of objectivity in both establishing and evaluating cybersecurity and data privacy controls. It draws upon the high-level structure of the Systems Security Engineering Capability Maturity Model v2.0 (SSE-CMM).
The SCR-CMM is meant to solve the problem of objectivity in both establishing and evaluating cybersecurity and data privacy controls. It draws upon the high-level structure of the .
A binary pass/fail assessment answers the question “Are we compliant?” The SCR-CMM answers a far more useful question: “How well are we actually doing this?” Compliance frameworks tell organizations what controls to implement, but they do not provide a meaningful way to measure whether those controls are implemented effectively, consistently, or sustainably.
There are many competing models that exist to demonstrate maturity. Given the available choices, the SCF decided to leverage an existing framework, rather than reinvent the wheel. In simple terms, we provided control-level criteria to an existing CMM model.
Four Core Objectives of the SCR-CMM
By using the term “nested,” we refer to how the SCR-CMM’s control criteria were written to acknowledge that each succeeding level of maturity is built upon its predecessor. Essentially, you cannot run without first learning how to walk.
This approach to defining cybersecurity & privacy control maturity is how the SCR-CMM is structured. The following two questions should be kept in mind when evaluating the maturity of a control (or Assessment Objective):
Do you need to answer “yes” to every bullet pointed criteria under a level of maturity? No. Every organization is different. The maturity criteria items associated with SCF controls are to help establish what would reasonably exist for each level of maturity. Fundamentally, the decision comes down to assessor experience, professional competence and common sense.
Maintaining the Integrity of Maturity-Based Criteria
Consciously designating a higher level of maturity (based on objective criteria) to make an organization appear more mature should be considered fraud. There is no room in cybersecurity and data protection operations for unethical parties.
While a more mature implementation of controls can equate to an increased level of security, higher maturity and higher assurance are not mutually inclusive. Maturity is simply a measure of governance activities pertaining to a specific control or set of controls.
According to NIST, assurance is “grounds for confidence that the set of intended security controls in an information system are effective in their application.” Increased rigor in control testing is what leads to increased assurance. Therefore, increased rigor and increased assurance are mutually inclusive.
Standard rigor assessments determine whether safeguards are implemented and free of obvious errors. This provides a minimum level of assurance.
Enhanced rigor assessments determine whether safeguards are implemented, free of obvious/apparent errors, and provide increased grounds for confidence that controls are implemented correctly and operating as intended.
Comprehensive rigor assessments provide further increased confidence that controls are implemented correctly, operating as intended on an ongoing and consistent basis, with support for continuous improvement.
The SCR-CMM uses six descriptive maturity levels drawn from the SSE-CMM v2.0 structure. Each level has specific observable criteria for what “implemented at this level” means for any given SCF control.
This level of maturity is defined as “non-existence practices,” where the control is not being performed:
L0 practices, or a lack thereof, are generally considered to be negligent. The reason for this is if a control is reasonably-expected to exist, by not performing the control that is negligent behavior. The need for the control could be due to a law, regulation or contractual obligation (e.g., client contract or industry association requirement).
Note – The reality with a L0 level of maturity is often:
This level of maturity is defined as “ad hoc practices,” where the control is being performed, but lacks completeness & consistency:
L1 practices are generally considered to be negligent. The reason for this is if a control is reasonably-expected to exist, by only implementing ad-hoc practices in performing the control that could be considered negligent behavior. The need for the control could be due to a law, regulation or contractual obligation (e.g., client contract or industry association requirement).
Note – The reality with a L1 level of maturity is often:
Practices are “requirements-driven” where the intent of control is met in some circumstances, but not standardized across the entire organization:
L2 practices are generally considered to be “audit ready” with an acceptable level of evidence to demonstrate due diligence and due care in the execution of the control. L2 practices are generally targeted on specific systems, networks, applications or processes that require the control to be performed for a compliance need (e.g., PCI DSS, HIPAA, CMMC, NIST 800-171, etc.).
Note – The reality with a L2 level of maturity is often:
This level of maturity is defined as “enterprise-wide standardization,” where the practices are well-defined and standardized across the organization:
L3 practices are generally considered to be “audit ready” with an acceptable level of evidence to demonstrate due diligence and due care in the execution of the control. Unlike L2 practices that are narrowly focused, L3 practices are standardized across the organization.
It can be argued that L3 practices focus on security over compliance, where compliance is a natural byproduct of those secure practices. These are well-defined and properly-scoped practices that span the organization, regardless of the department or geographic considerations.
Note – The reality with a L3 level of maturity is often:
This level of maturity is defined as “metrics-driven practices,” where in addition to being well-defined and standardized practices across the organization, there are detailed metrics to enable governance oversight:
L4 practices are generally considered to be “audit ready” with an acceptable level of evidence to demonstrate due diligence and due care in the execution of the control, as well as detailed metrics enable an objective oversight function. Metrics may be daily, weekly, monthly, quarterly, etc.
Note – The reality with a L4 level of maturity is often:
Detailed measures of performance are collected and analyzed. This leads to a quantitative understanding of process capability and an improved ability to predict performance.
L5 practices are generally considered to be “audit ready” with an acceptable level of evidence to demonstrate due diligence and due care in the execution of the control and incorporates a capability to continuously improve the process. Interestingly, this is where Artificial Intelligence (AI) and Machine Learning (ML) would exist, since AI/ML would focus on evaluating performance and making continuous adjustments to improve the process. However, AI/ML are not required to be L5.
Note – The reality with a L5 level of maturity is often:
For most organizations, the “sweet spot” for maturity targets is between L2 and L4 levels. What defines the ideal target is generally based on resource limitations and other business constraints.
Without the ability to demonstrate evidence of both due care and due diligence, an organization may be found negligent. The "negligence threshold" is between L1 and L2. At L2, practices are formalized to the point that documented evidence exists.
Risk associated with the control in question decreases with maturity, but noticeable risk reductions are harder to attain above L3. Oversight and process automation can decrease risk, but generally not as noticeably as steps taken to attain L3.
Process improvements increase with maturity, based on shorter review cycles and increased process oversight. What might have been an annual review cycle can be near real-time with AI and Machine Learning.
Perceived value of security controls increases with maturity. However, perceived value tends to decrease after L3 since the additional cost and complexity becomes harder to justify to business stakeholders.
Internal vs External Maturity Shift
L0–L3 are “internal” maturity levels for cybersecurity and data privacy teams, whereas L4–L5 are “external” maturity levels that expand beyond those teams. It isn’t until L4–L5 where there is true business stakeholder involvement in oversight and process improvement.
The SCR-CMM is used across the entire GRC lifecycle, from establishing program expectations through ongoing evaluation and due diligence.
Provide CISO/CIOs with objective criteria that can be used to establish expectations for a cybersecurity & privacy program. The SCR-CMM defines what “good enough” looks like at each maturity level, eliminating subjective interpretations.
Provide objective criteria for project teams so that secure, compliant and resilient practices are appropriately planned and budgeted for. Maturity targets translate directly into resource requirements and timelines.
Provide objective criteria to evaluate External Service Provider (ESP) practices. The SCR-CMM provides a standardized measurement framework for third-party risk assessments and vendor due diligence.
Provide a means to perform due diligence of cybersecurity and data privacy capabilities as part of MA&D activities. Maturity scores provide an objective, defensible assessment of an acquisition target’s security posture.
Assessors/auditors are expected to review artifacts and other evidence to independently verify that an organization meets the intent for all applicable controls. There are three assessment methods:
The process of checking, inspecting, reviewing, observing, studying or analyzing one or more assessment objects to facilitate understanding, achieve clarification or obtain evidence.
The process of conducting discussions with individuals or groups in an organization to facilitate understanding, achieve clarification or lead to the location of evidence.
The process of exercising one or more assessment objects under specified conditions to compare actual with expected behavior.
The SCR-CMM is designed to operate within a continuous PDCA improvement cycle, enabling organizations to systematically advance control maturity over time.
Define the assessment scope. Select the SCF control subset applicable to your organization’s risk tier and regulatory obligations. Define target CMM levels for each domain based on regulatory requirements and risk appetite.
Conduct the CMM assessment. Score each control using the built-in L0–L5 criteria in the SCF spreadsheet. Gather evidence using the ERL. Document gaps, assign owners, and define remediation timelines for controls below target level.
Calculate domain-level and program-level maturity scores. Compare against prior assessment results to measure improvement. Validate that remediation actions have raised CMM scores as planned. Report results to management.
Update remediation plans for remaining gaps. Set new target CMM levels for the next cycle. Advance controls that reached their target level toward the next level. Incorporate findings into the security roadmap and budget planning.
The SCR-CMM and SCR-RMM are companion models. Maturity measurement and risk management work together within the same SCF-based program framework.
Defines how to measure and score control implementation maturity, providing the measurement system that tells the organization how well each control is implemented.
Six maturity levels (L0 Not Performed → L5 Continuously Improving)
Observable criteria for every SCF control
Based on SSE-CMM v2.0 structure (ISO/IEC 21827)
Evidence-based, not self-reported opinion
Defines how to identify, assess, and treat cybersecurity risk, providing the risk management framework that determines which controls matter most and how to allocate resources.
Structured risk identification & assessment
Risk treatment planning & tracking
Integrates with SCR-CMM maturity scoring
Built on the SCF control catalog