Set Theory Relationship Mapping (STRM)
Starting with release 2024.1, the SCF now leverages the Set Theory Relationship Mapping (STRM) for crosswalk mapping, since STRM is generally well-suited to evaluate cybersecurity and data privacy laws, regulations and frameworks. With the publishing of NIST IR 8477, Mapping Relationships Between Documentary Standards, Regulations, Frameworks, and Guidelines: Developing Cybersecurity and Privacy Concept Mappings it establishes the US Government's playbook for how to perform crosswalk mapping between different cybersecurity and data privacy laws, regulations and frameworks. This document is part of NIST’s broader NIST OLIR Program that is an “effort to facilitate Subject Matter Experts (SMEs) in defining standardized online informative references (OLIRs) between elements of their documents, products, and services and elements of NIST documents…” The SCF currently participates in the National Online Informative References (OLIR) Program and with NIST's preference for STRM, we decided an aligned crosswalk mapping methodology makes sense.
NIST IR 8477 Crosswalk Mapping
What NIST IR 8477 does is provide the “gold standard” practice for how an individual can perform crosswalk mapping with no technology needed, where it can literally be performed with a pencil and piece of paper. Children learn the process of diagramming sentences in grade school (e.g., Reed–Kellogg model) with pencils and paper. This is the process of graphically identifying nouns, verbs, adjectives and modifiers to teach proper sentence structure for how various components of language work together to communicate an idea. With the advent of Artificial Intelligence (AI), the ability to diagram sentences in both computer and human-readable format is achievable through Natural Language Processing (NLP). From a cybersecurity crosswalking perspective, NLP can be used to evaluate a control statement (e.g., must have firewall) to identify the noun (e.g., firewall) and verb (e.g., must have) to determine the relative strength it maps to a different control (e.g., shall have network defense appliances). Where that becomes interesting is both in protecting the underlying content (e.g., Intellectual Property (IP)) and patentability.
Expert-Derived Content (EDC) vs Natural Language Processing (NLP)
While the SCF leverages expert-derived content (e.g., human subject-matter experts), other solutions use NLP to create their crosswalk mapping. One significant downside for those solutions leveraging NLP is their forfeit of IP since AI-generated content is currently prohibited from copyright protections due to the content not being the work of a human creator. Therefore, NLP-generated content could be considered free content from an IP perspective, since a copyright of AI-generated content would not be enforceable.
Where it gets even more fascinating with AI-based solutions in the compliance space is with patentability for inventions due to the "mental steps" doctrine. In 2014, the US Supreme Court ruled that inventions are ineligible for patenting if the patent claim is something a human could do in their mind or with paper and pencil (e.g., a human performing sentence diagramming on a piece of paper and comparing the results of that sentence diagram with another). That landmark case (Alice Corp. v. CLS Bank International) established a new uncertainty about patent eligibility of AI and machine learning technologies. The result of Alice is that patents issued for compliance solutions leveraging NLP to perform crosswalk mapping may not hold up to scrutiny by the Patent Trial and Appeal Board (PTAB) given NIST published a document that describes how to perform crosswalk mapping without the assistance of technology.
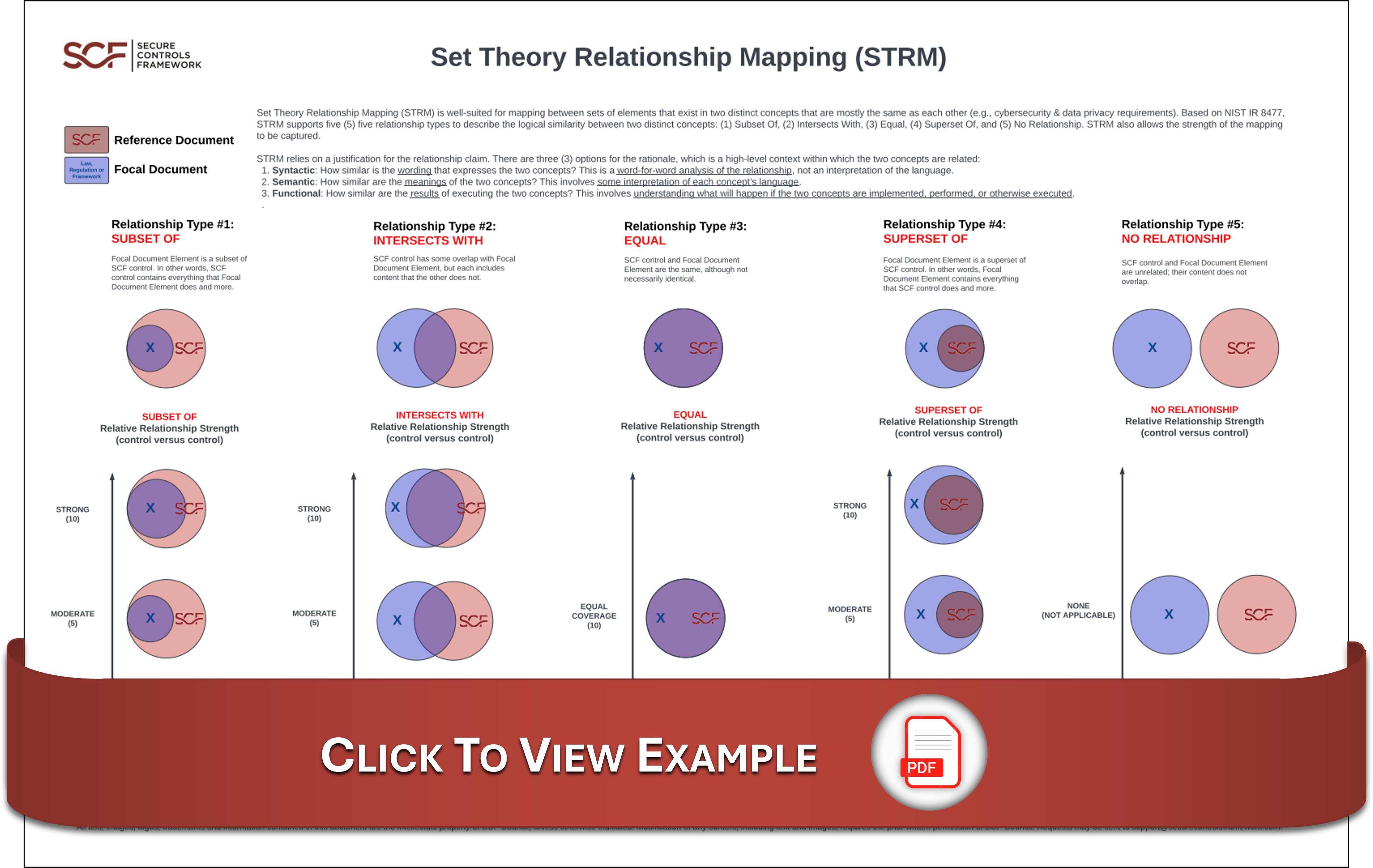
How The SCF Is Utilizing STRM
You can click on the image below to see a PDF version of how the SCF is utilizing STRM, as well as an example for what that looks like with a few NIST CSF 2.0 controls:
STRM Downloads
You can purchase Excel versions of the Set Theory Relationship Mappings (STRM) mappings at the SCF Store.
The current list of Set Theory Relationship Mappings (STRM) include the following:
General Frameworks
- AICPA Privacy Management Framework (PMF) (2020): https://content.securecontrolsframework.com/strm/scf-strm-general-aicpa-pmf-2020.pdf
- Trust Services Criteria (TSC) (2017): https://content.securecontrolsframework.com/strm/scf-strm-general-aicpa-tsc-2017.pdf
- APEC Privacy Framework (2015): https://content.securecontrolsframework.com/strm/scf-strm-general-apec-privacy-framework-2015.pdf
- Standard 200-1 (v1.0): https://content.securecontrolsframework.com/strm/scf-strm-general-bsi-200-1-1-0.pdf
- Critical Security Controls (CSC) (v8.1): https://content.securecontrolsframework.com/strm/scf-strm-general-cis-csc-8-1.pdf
- Critical Security Controls (CSC) (v8.1) - IG1: https://content.securecontrolsframework.com/strm/scf-strm-general-cis-csc-8-1-ig1.pdf
- Critical Security Controls (CSC) (v8.1) - IG2: https://content.securecontrolsframework.com/strm/scf-strm-general-cis-csc-8-1-ig2.pdf
- Critical Security Controls (CSC) (v8.1) - IG3: https://content.securecontrolsframework.com/strm/scf-strm-general-cis-csc-8-1-ig3.pdf
- Control Objectives for Information and Related Technologies (COBIT) (2019): https://content.securecontrolsframework.com/strm/scf-strm-general-cobit-2019.pdf
- Committee of Sponsoring Organizations (COSO) (2013): https://content.securecontrolsframework.com/strm/scf-strm-general-coso-2013.pdf
- Cloud Controls Matrix (CCM) (v4.1.0): https://content.securecontrolsframework.com/strm/scf-strm-general-csa-cmm-4-1-0.pdf
- IoT Security Controls Framework (v2): https://content.securecontrolsframework.com/strm/scf-strm-general-csa-iot-2.pdf
- Cyber Resilience Capability Maturity Model (CR-CMM) (2026): https://content.securecontrolsframework.com/strm/scf-strm-general-cr-cmm-2026.pdf
- GovRAMP: https://content.securecontrolsframework.com/strm/scf-strm-general-govramp.pdf
- GovRAMP Core: https://content.securecontrolsframework.com/strm/scf-strm-general-govramp-core.pdf
- GovRAMP Low: https://content.securecontrolsframework.com/strm/scf-strm-general-govramp-low.pdf
- GovRAMP Low+: https://content.securecontrolsframework.com/strm/scf-strm-general-govramp-low-plus.pdf
- GovRAMP Moderate: https://content.securecontrolsframework.com/strm/scf-strm-general-govramp-mod.pdf
- GovRAMP High: https://content.securecontrolsframework.com/strm/scf-strm-general-govramp-high.pdf
- IEC TR 60601-4-5 (2021): https://content.securecontrolsframework.com/strm/scf-strm-general-iec-tr-60601-4-5-2021.pdf
- IEC 62443-2-1 (2024): https://content.securecontrolsframework.com/strm/scf-strm-general-iec-62443-2-1-2024.pdf
- IEC 62443-3-3 (2013): https://content.securecontrolsframework.com/strm/scf-strm-general-iec-62443-3-3-2013.pdf
- IEC 62443-4-1 (2018): https://content.securecontrolsframework.com/strm/scf-strm-general-iec-62443-4-1-2018.pdf
- IEC 62443-4-2 (2019): https://content.securecontrolsframework.com/strm/scf-strm-general-iec-62443-4-2-2019.pdf
- International Maritime Organization (IMO) Guidelines on Maritime Cyber Risk Management (2025): https://content.securecontrolsframework.com/strm/scf-strm-general-imo-maritime-cyber-risk-management-2025.pdf
- ISO 21434 (2021): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-21434-2021.pdf
- ISO 22301 (2019): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-22301-2019.pdf
- ISO 27001 (2022): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-27001-2022.pdf
- ISO 27002 (2022): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-27002-2022.pdf
- ISO 27017 (2015): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-27017-2015.pdf
- ISO 27018 (2025): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-27018-2025.pdf
- ISO 27701 (2025): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-27701-2025.pdf
- ISO 29100 (2024): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-29100-2024.pdf
- ISO 31000 (2018): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-31000-2018.pdf
- ISO 31010 (2009): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-31010-2009.pdf
- ISO 42001 (2023): https://content.securecontrolsframework.com/strm/scf-strm-general-iso-42001-2023.pdf
- MITRE ATT&CK (v16.1): https://content.securecontrolsframework.com/strm/scf-strm-general-mitre-att&ck-16-1.pdf
- Content Security Best Practices Common Guidelines (v5.3.1): https://content.securecontrolsframework.com/strm/scf-strm-general-mpa-csbp-5-3-1.pdf
- Insurance Data Security Model Law 668 (2017): https://content.securecontrolsframework.com/strm/scf-strm-general-naic-insurance-data-security-model-law-668-2017.pdf
- NIST AI 100-1 (AI RMF 1.0): https://content.securecontrolsframework.com/strm/scf-strm-general-nist-100-1-ai-rmf.pdf
- NIST AI 600-1: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-600-1-gen-ai-profile.pdf
- NIST Privacy Framework (v1.0): https://content.securecontrolsframework.com/strm/scf-strm-general-nist-privacy-framework-1-0.pdf
- NIST SP 800-37 R2: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-37-r2.pdf
- NIST SP 800-39: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-39.pdf
- NIST SP 800-53 R5: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-53-r5-2.pdf
- NIST SP 800-53 R5 - Privacy Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-53-r5-2-privacy.pdf
- NIST SP 800-53 R5 - Low Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-53-r5-2-low.pdf
- NIST SP 800-53 R5 - Moderate Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-53-r5-2-mod.pdf
- NIST SP 800-53 R5 - High Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-53-r5-2-high.pdf
- NIST SP 800-66 R2: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-66-r2.pdf
- NIST SP 800-82 R3: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-82-r3.pdf
- NIST SP 800-82 R3 - Low OT Overlay: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-82-r3-low.pdf
- NIST SP 800-82 R3 - Moderate OT Overlay: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-82-r3-mod.pdf
- NIST SP 800-82 R3 - High OT Overlay: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-82-r3-high.pdf
- NIST SP 800-160 (Vol 2, Rev 1): https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-160-vol-2-r1.pdf
- NIST SP 800-161 R1 UDP1: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-161-r1.pdf
- NIST SP 800-161 R1 UDP1 - C-SCRM Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-161-r1-cscrm.pdf
- NIST SP 800-161 R1 UDP1 - Flow Down Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-161-r1-flowdown.pdf
- NIST SP 800-161 R1 UDP1 - Level 1 Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-161-r1-level-1.pdf
- NIST SP 800-161 R1 UDP1 - Level 2 Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-161-r1-level-2.pdf
- NIST SP 800-161 R1 UDP1 - Level 3 Baseline: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-161-r1-level-3.pdf
- NIST SP 800-171 R2: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-171-r2.pdf
- NIST SP 800-171 R3: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-171-r3.pdf
- NIST SP 800-171A: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-171a.pdf
- NIST SP 800-171A R3: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-171a-r3.pdf
- NIST SP 800-172: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-172.pdf
- NIST SP 800-207: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-207.pdf
- NIST SP 800-218: https://content.securecontrolsframework.com/strm/scf-strm-general-nist-800-218.pdf
- NIST Cybersecurity Framework (v2.0): https://content.securecontrolsframework.com/strm/scf-strm-general-nist-csf-2-0.pdf
- OECD Privacy Principles (2010): https://content.securecontrolsframework.com/strm/scf-strm-general-oecd-privacy-principles-2010.pdf
- OWASP Top 10 (2025): https://content.securecontrolsframework.com/strm/scf-strm-general-owasp-top-10-2025.pdf
- Payment Card Industry Data Security Standard (PCI DSS) (v4.01): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ A (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-a.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ A-EP (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-a-ep.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ B (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-b.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ B-IP (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-b-ip.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ C (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-c.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ C-VT (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-c-vt.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ D Merchant (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-d-merchant.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ D Service Provider (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-d-service-provider.pdf
- Payment Card Industry Data Security Standard (PCI DSS) - SAQ P2PE (v4.0.1): https://content.securecontrolsframework.com/strm/scf-strm-general-pci-dss-4-0-1-saq-p2pe.pdf
- Data Privacy Management Principle (DPMP) (2025): https://content.securecontrolsframework.com/strm/scf-strm-general-scf-dpmp-2025.pdf
- SPARTA Countermeasures: https://content.securecontrolsframework.com/strm/scf-strm-general-sparta.pdf
- SWIFT Customer Security Controls Framework (2025): https://content.securecontrolsframework.com/strm/scf-strm-general-swift-cscf-2025.pdf
- TISAX ISA (6.0.3): https://content.securecontrolsframework.com/strm/scf-strm-general-tisax-6-0-3.pdf
- UL 2900-1 (2017): https://content.securecontrolsframework.com/strm/scf-strm-general-ul-2900-1-2017.pdf
- UL 2900-2-2 (2016): https://content.securecontrolsframework.com/strm/scf-strm-general-ul-2900-2-2-2016.pdf
- UN Regulation No. 155 (2021): https://content.securecontrolsframework.com/strm/scf-strm-general-un-155-2021.pdf
- UNECE WP.29 (2020): https://content.securecontrolsframework.com/strm/scf-strm-general-un-ece-wp-29-2020.pdf
United States Specific Laws & Regulations
- CERT-RMM (v1.2): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-cert-rmm-1-2.pdf
- Children's Online Privacy Protection Act (COPPA) (2024): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-law-coppa-2024.pdf
- CISA Secure Software Development Attestation Form (SSDAF) (2024): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dhs-cisa-ssdaf-2024.pdf
- CISA Trusted Internet Connections 3.0 Security Capabilities Catalog (TIC 3.0): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dhs-cisa-tic-3-0.pdf
- CISA Cross-Sector Cybersecurity Performance Goals (CPG) (2.0): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dhs-cisa-cpg-2-0.pdf
- Criminal Justice Information Services (CJIS) Security Policy (v6.0): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-fbi-cjis-6-0.pdf
- Cybersecurity Capability Maturity Model (C2M2) (v2.1): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-doe-c2m2-2-1.pdf
- Cybersecurity Maturity Model Certification (CMMC) 2.0 - Level 1: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-cmmc-2-level-1.pdf
- Cybersecurity Maturity Model Certification (CMMC) 2.0 - Level 1 Assessment Objectives: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-cmmc-2-level-1-aos.pdf
- Cybersecurity Maturity Model Certification (CMMC) 2.0 - Level 2: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-cmmc-2-level-2.pdf
- Cybersecurity Maturity Model Certification (CMMC) 2.0 - Level 3: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-cmmc-2-level-3.pdf
- Data Privacy Framework (2023): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-doc-data-privacy-framework-2023.pdf
- Department of War (DoW) - Zero Trust Execution Roadmap (v1.1): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-zt-roadmap-1-1.pdf
- Department of War (DoW) - Zero Trust Reference Architecture (v2): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-zta-reference-architecture-2-0.pdf
- DFARS 252.204-7012: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-dfars-252-204-7012.pdf
- Executive Order 14028 - Improving the Nation's Cybersecurity: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-eo-14028.pdf
- Fair & Accurate Credit Transactions Act (FACTA) & Fair Credit Reporting Act (FCRA) (2023): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-law-facta-fcra-2023.pdf
- FAR 52.204-21: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-far-52-204-21.pdf
- FAR 52.204-25 (NDAA Section 889): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-far-52-204-25.pdf
- FAR 52.204-27: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-far-52-204-27.pdf
- Farm Credit Administration (FCA) Cyber Risk Management (2023): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-sro-fca-crm-2023.pdf
- Food & Drug Administration (FDA) 21 CFR Part 11 (2025): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-fda-21-cfr-part-11-2025.pdf
- FedRAMP R5 - Low Baseline: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-gsa-fedramp-5-low.pdf
- FedRAMP R5 - Moderate Baseline: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-gsa-fedramp-5-mod.pdf
- FedRAMP R5 - High Baseline: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-gsa-fedramp-5-high.pdf
- FedRAMP R5 - Li-SAAS Baseline: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-gsa-fedramp-5-li-saas.pdf
- Family Educational Rights and Privacy Act (FERPA) (2010): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-law-ferpa-2010.pdf
- FINRA Cybersecurity Rules: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-sro-finra.pdf
- US Fair Information Practice Principles (FIPPs) (1973): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-omb-fipps-1973.pdf
- Federal Trade Commission (FTC) Act: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-law-ftc-act.pdf
- Gramm Leach Bliley Act (GLBA) (2023): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-law-glba-cfr-314-2023.pdf
- HHS § 155.260 (2016): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-hhs-45-cfr-155-260-2016.pdf
- HIPAA Administrative Simplification (2013): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-law-hipaa-simplification-2013.pdf
- HIPAA Security Rule (2013): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-law-hipaa-security-rule-2013.pdf
- IRS 1075 (2021): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-irs-1075-2021.pdf
- MARS-E Document Suite (2.0): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-cms-marse-2-0.pdf
- NERC Critical Infrastructure Protection (CIP) (2024): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-nerc-cip-2024.pdf
- National Industrial Security Program Operating Manual (NISPOM) (2020): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-nispom-2020.pdf
- Safeguarding of NNPI (2010): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-dow-safeguarding-nnpi-2010.pdf
- SEC Cybersecurity Rule (2023): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-sec-cybersecurity-rule-2023.pdf
- SOX (2002): https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-law-sox-2002.pdf
- TSA Security Directive 1580/82-2022-01: https://content.securecontrolsframework.com/strm/scf-strm-usa-federal-tsa-security-directive-1580-82-2022-01.pdf
- State - Alaska Personal Information Protection Act (PIPA) (2009): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-ak-pipa-2009.pdf
- State - California SB327 (2018): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-ca-sb327-2018.pdf
- State - California Consumer Privacy Act (CCPA) (2026): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-ca-ccpa-cpra-2026.pdf
- State - California SB1386 (2002): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-ca-sb1386-2002.pdf
- State - Colorado Privacy Act (2021): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-co-privacy-act-2021.pdf
- State - Illinois Biometric Information Privacy Act (BIPA) (2008): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-il-bipa-2008.pdf
- State - Illinois Identity Protection Act (IPA) (2009): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-il-ipa-2009.pdf
- State - Illinois Personal Information Protection Act (PIPA) (2006): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-il-pipa-2006.pdf
- State - Massachusetts 201 CMR 17.00 (2008): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-ma-201-cmr-17-2008.pdf
- State - Nevada Privacy Law (2023): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-nv-privacy-law-2023.pdf
- State - Nevada Operation of Gaming Establishment (NOGE) Regulation 5.260 (2024): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-nv-regulation-5-2024.pdf
- State - Nevada SB220 (2019): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-nv-sb220-2019.pdf
- State - New York Department of Financial Services 23NYCRR Part 500 (2023 Amendment 2): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-ny-dfs-23-nycrr500-2023-amd2.pdf
- State - New York SHIELD Act (SB S5575B) (2019): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-ny-shield-act-2019.pdf
- State - Oregon Consumer Information Protection Act (ORS 646A) (2025): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-or-ors-646a-2025.pdf
- State - Oregon Consumer Privacy Act (SB 619) (2023): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-or-cpa-2023.pdf
- State - Tennessee Information Protection Act (TIPA) (2025): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-tn-tipa-2025.pdf
- State - Texas Identity Theft Enforcement and Protection Act (BC521) (2009): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-tx-bc521-2009.pdf
- State - Texas Consumer Data Protection Act (2025): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-tx-cdpa-2025.pdf
- State - Texas DIR Security Control Standards Catalog (v2.2): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-tx-dir-security-control-standards-catalog-2-2.pdf
- State - Texas SB820 (2019): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-tx-sb820-2019.pdf
- State - Texas Safe Harbor Law (SB2610) (2025): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-tx-sb2610-2025.pdf
- State - TX-RAMP 2.0 - Level 1: https://content.securecontrolsframework.com/strm/scf-strm-usa-state-tx-txramp-2-0-level-1.pdf
- State - TX-RAMP 2.0 - Level 2: https://content.securecontrolsframework.com/strm/scf-strm-usa-state-tx-txramp-2-0-level-2.pdf
- State - Virginia Consumer Data Protection Act (2023): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-va-cdpa-2023.pdf
- State - Vermont Data Broker Registration Act (Act 171 of 2018): https://content.securecontrolsframework.com/strm/scf-strm-usa-state-vt-act-171-2018.pdf
Europe, Middle East & Africa (EMEA)
- EU Artificial Intelligence Act (AI Act) (2024): https://content.securecontrolsframework.com/strm/scf-strm-emea-eu-ai-act-2024.pdf
- EU Cyber Resilience Act (CRA) (2022): https://content.securecontrolsframework.com/strm/scf-strm-emea-eu-cyber-resilience-act-2022.pdf
- EU Cyber Resilience Act Annexes (CRA Annexes) (2022): https://content.securecontrolsframework.com/strm/scf-strm-emea-eu-cyber-resilience-act-annexes-2022.pdf
- EU Digital Operational Resilience Act (DORA) (2023): https://content.securecontrolsframework.com/strm/scf-strm-emea-eu-dora-2023.pdf
- EU General Data Protection Regulation (GDPR) (2016): https://content.securecontrolsframework.com/strm/scf-strm-emea-eu-gdpr-2016.pdf
- EU NIS2 Directive (2022): https://content.securecontrolsframework.com/strm/scf-strm-emea-eu-nis2-2022.pdf
- EU NIS2 Annex (2024): https://content.securecontrolsframework.com/strm/scf-strm-emea-eu-nis2-annex-2024.pdf
- Saudi Arabia - Cybersecurity Guidelines for Internet of Things (CGIoT-1:2024): https://content.securecontrolsframework.com/strm/scf-strm-emea-sau-cgiot-2024.pdf
- Saudi Arabia - Personal Data Protection Law (PDPL) (2023): https://content.securecontrolsframework.com/strm/scf-strm-emea-sau-pdpl-2023.pdf
- Spain - BOE-A-2022-7191: https://content.securecontrolsframework.com/strm/scf-strm-emea-esp-boe-a-2022-7191.pdf
- UAE - National Information Assurance Framework (NIAF) (2023): https://content.securecontrolsframework.com/strm/scf-strm-emea-uae-niaf-2023.pdf
- UK - Cyber Assessment Framework (CAF) (v4.0): https://content.securecontrolsframework.com/strm/scf-strm-emea-gbr-caf-4-0.pdf
- UK - Defstan 05-138 (2024): https://content.securecontrolsframework.com/strm/scf-strm-emea-gbr-def-stan-05-138-2024.pdf
- UK - Defstan 05-138 (2024) - L0: https://content.securecontrolsframework.com/strm/scf-strm-emea-gbr-def-stan-05-138-l0-2024.pdf
- UK - Defstan 05-138 (2024) - L1: https://content.securecontrolsframework.com/strm/scf-strm-emea-gbr-def-stan-05-138-l1-2024.pdf
- UK - Defstan 05-138 (2024) - L2: https://content.securecontrolsframework.com/strm/scf-strm-emea-gbr-def-stan-05-138-l2-2024.pdf
- UK - Defstan 05-138 (2024) - L3: https://content.securecontrolsframework.com/strm/scf-strm-emea-gbr-def-stan-05-138-l3-2024.pdf
Asia Pacific (APAC)
- Australia - Essential Eight (2024): https://content.securecontrolsframework.com/strm/scf-strm-apac-aus-essential-8-2024.pdf
- Australia - Information Security Manual (ISM) (June 2024): https://content.securecontrolsframework.com/strm/scf-strm-apac-aus-ism-2024-june.pdf
- China - Cybersecurity Law (2017): https://content.securecontrolsframework.com/strm/scf-strm-apac-chn-cybersecurity-law-2017.pdf
- India - DPDPA (2023): https://content.securecontrolsframework.com/strm/scf-strm-apac-ind-dpdpa-2023.pdf
- India - SEBI CSCRF (2024): https://content.securecontrolsframework.com/strm/scf-strm-apac-ind-sebi-2024.pdf
- Japan - Information System Security Management and Assessment Program (ISMAP) - https://content.securecontrolsframework.com/strm/scf-strm-apac-jpn-ismap.pdf
- New Zealand - HISF MLHSP (2023): https://content.securecontrolsframework.com/strm/scf-strm-apac-nzl-hisf-mlhsp-2023.pdf
- New Zealand - HISF MicroSmall (2023): https://content.securecontrolsframework.com/strm/scf-strm-apac-nzl-hisf-microsmall-2023.pdf
- New Zealand - HISF Guidance for Suppliers (2023): https://content.securecontrolsframework.com/strm/scf-strm-apac-nzl-hisf-suppliers-2023.pdf
Americas (Non-USA)
- Canada - OSFI B-13 (2022): https://content.securecontrolsframework.com/strm/scf-strm-americas-can-osfi-b13-2022.pdf
- Canada - ITSP.10.171 (2025): https://content.securecontrolsframework.com/strm/scf-strm-americas-can-itsp-10-171-2025.pdf
The SCF welcomes community involvement and we provide the ability for community-suggested mapping. The SCF Council provides a downloadable SCF Community STRM Template, that SCF Practitioners can then use to perform their own STRM and submit it to the SCF Council, where it can be evaluated for the possible inclusion in a future SCF release.
Step 1. Define The Focal Document To Be Mapped
We are not here to teach you STRM, so if you want to participate in any community mapping, it is expected that you (1) are very familiar the practices described in NIST IR 8477 and (2) possess the professional competence to conduct crosswalk mapping in accordance with those principles.
The first tab on the STRM template is called "STRM Overview" and there are two highlighted cells near the top of the sheet: the focal document cell and the focal document URL cell.
- In the focal document cell, you must provide the official name of the law, regulation, or framework you are providing mapping for.
- In the focal document URL cell, you must provide a valid hyperlink where the focal document can be downloaded.
Without either of these two pieces of information, the SCF Council will not review your STRM submission.
Step 2. Perform STRM
The second tab of the STRM template is called "Community STRM submission." This is purposely left as a blank template for you to perform your crosswalk mapping:
- Column A is the Focal Document Element #. This is the specific law, regulation, or framework control number. This is a mandatory field. Without a unique FDE value, there is no granularity and means there is nothing that can be mapped to.
- Column B is the Focal Document Element Name. Most laws, regulations and frameworks do not have FDE names, so this is required only if it is available.
- Column C is the Focal Document Element Description. This is the actual text of the law, regulation, or framework. Essentially, it is a cut & paste effort to populate this cell.
- Column D is the proposed SCF Control Name that you feel maps to the Focal Document Element.
- Column E is tied to Column D. This is the SCF control number.
- Column F is tied to Column D. This is the SCF control description.
- Column G is the proposed STRM relationship. There are only 5 options. The relationship can be (1) a Subset Of, (2) Intersects With, (3) Equal to, (4) a Superset Of, or (5) there is No Relationship.
- Column H is the proposed strength of the STRM relationship that has a 1 to 10 rating. A rating of 1 indicates a nominal relationship, a rating of 5 indicates a moderately strong relationship, and a rating of 10 indicates a strong relationship. Realistically, a rating of 10 is going to be given if the STRM relationship is either equal to or where the F-D-E is a subset of the SCF control.
- Column I is an optional notes section where you can provide textual justification for your recommendations.
Step 3. Submit To SCF Council
Once you complete your STRM exercise, you can then email it to the SCF Council for review. Just email the Excel spreadsheet as an attachment to [email protected].